For any business operating in Georgia's dynamic economic landscape, enterprise data destruction is the final, non-negotiable step in the IT asset lifecycle. It is the formal, documented process of ensuring that sensitive information on retired servers, company laptops, and hard drives is permanently and verifiably eliminated. This is not about simply hitting 'delete'; it is a fundamental security practice that protects your enterprise from catastrophic data breaches, ensures regulatory compliance, and safeguards your brand's hard-earned reputation. For businesses in Georgia, a secure data destruction strategy is a core component of modern risk management.
Why Secure Data Destruction is a Mandate for Georgia Enterprises
For companies across Georgia, from bustling Atlanta to other commercial hubs, managing end-of-life data is not merely an IT task—it is a critical line of defense. The state's significant economic growth has led to an explosion in the volume of sensitive corporate and customer data being generated, stored, and ultimately retired.
This data proliferation has cemented Georgia's position on the global technology stage. The Atlanta metro area, in particular, has rapidly emerged as a leading data center market. The sheer scale of this infrastructure highlights the immense amount of critical business information that resides within our state, making enterprise data destruction in Georgia a top priority for IT and security leaders.
The Tangible Risks of Inadequate Disposal
Disposing of old hard drives or servers without certified destruction is a high-stakes gamble with severe and predictable consequences. For any Georgia business, the potential fallout is significant.
- Devastating Data Breaches: A single improperly discarded hard drive can be a treasure trove for malicious actors, containing everything from confidential customer PII and financial records to invaluable trade secrets.
- Costly Regulatory Penalties: Federal regulations such as the FTC Disposal Rule and industry-specific mandates like HIPAA and GLBA impose steep financial penalties for non-compliance in data destruction.
- Irreparable Brand Damage: A public data breach can instantly shatter the trust built with customers and partners. The damage to your company’s reputation often inflicts more long-term financial harm than the initial fine.
Transforming a Liability into a Managed Process
This guide provides a framework for building a secure, compliant, and logical strategy for your end-of-life IT assets. The correct approach transforms a significant potential liability into a streamlined, documented business process.
By implementing a robust enterprise data destruction Georgia program with a certified partner, you proactively protect your organization's most valuable asset: its information. Our detailed guide on secure data destruction in Georgia offers further insights into building a compliant and effective program. Partnering with a certified local expert like Beyond Surplus ensures your security and compliance obligations are met, allowing your team to focus on core business objectives.
Choosing the Right Data Destruction Method for Your Assets
When it is time to retire enterprise IT assets, you are faced with a fundamental decision: secure data sanitization for reuse or complete physical destruction. The appropriate method depends entirely on your internal security policies, compliance requirements, and whether the hardware itself retains any financial value.
A sound enterprise data destruction Georgia strategy is not a one-size-fits-all solution. It requires matching the destruction technique to the asset's data sensitivity and potential for value recovery.
Wiping: Secure Sanitization for Value Recovery
Software-based data wiping, or sanitization, is the process of using certified software to overwrite every sector of a hard drive or SSD with random data. This process is often repeated in multiple passes, rendering the original information forensically unrecoverable.
This sanitization process adheres to rigorous standards like the NIST 800-88 Guidelines for Media Sanitization. It is the ideal method for newer, functional equipment that you intend to resell or redeploy internally. Data wiping preserves the hardware’s value, enabling a return on investment without compromising data security.
Shredding: The Definitive Method for Absolute Destruction
Physical destruction represents the highest level of data security, leaving absolutely no possibility of data recovery. It is the gold standard for devices at their end-of-life, those that are non-functional, or any media that contained your most sensitive intellectual property, financial data, or customer information.
The most common and trusted form of physical destruction is hard drive shredding. Industrial shredders mechanically grind hard drives, SSDs, backup tapes, and other media into small, mangled fragments. Once a drive is shredded, the data is irretrievably destroyed.
Another method, degaussing, uses a powerful magnetic field to erase data from magnetic media like traditional hard drives and tapes. While effective for that specific technology, it is crucial to note that degaussing is ineffective on modern Solid-State Drives (SSDs), which do not store data magnetically.
This decision tree helps visualize the appropriate path for your assets.
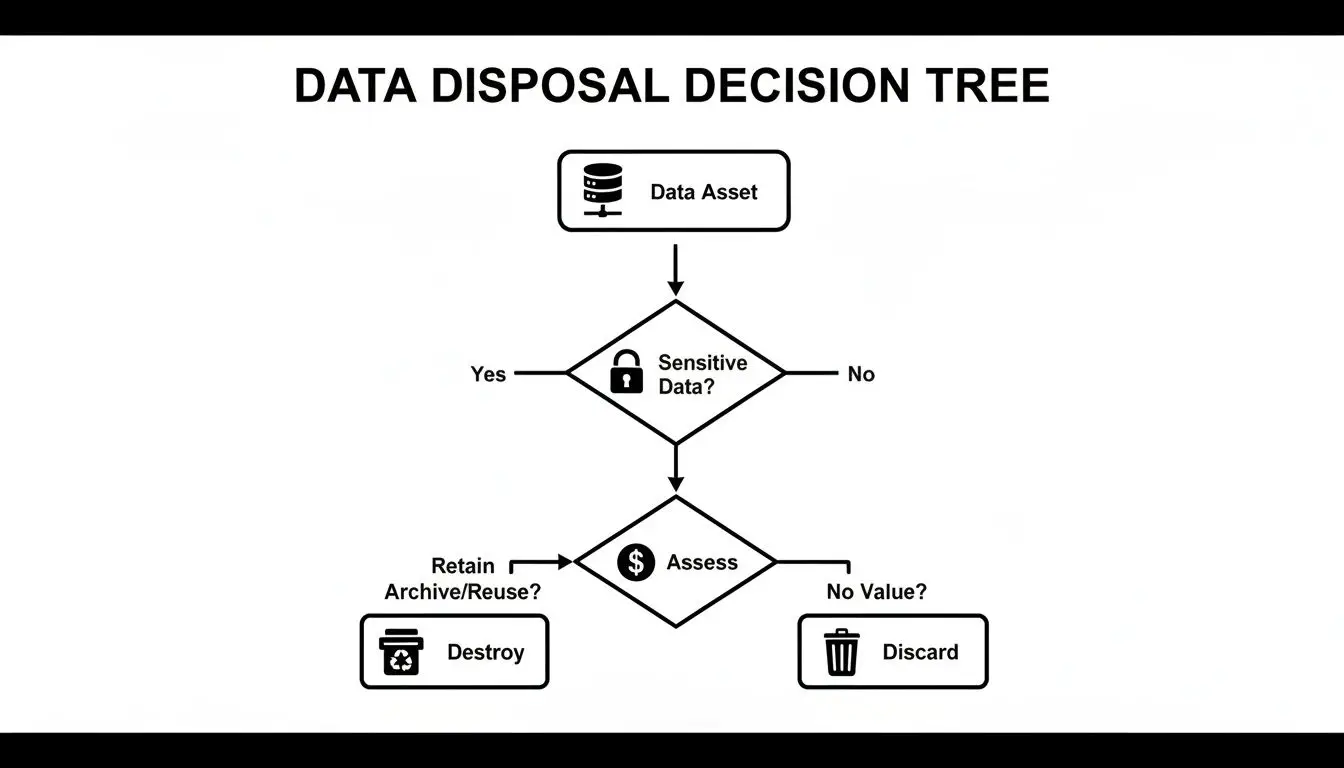
As shown, the presence of sensitive data makes secure destruction the default, safest path. If no sensitive data is present, the asset can be evaluated for value recovery.
Comparing Data Destruction Methods
To clarify the choice, this table breaks down how the primary methods compare for Georgia businesses.
| Method | Security Level | Media Reusability | Best For |
|---|---|---|---|
| Wiping | Very High | Yes | Newer laptops, PCs, and servers planned for resale or redeployment. |
| Degaussing | High | No | Older magnetic hard drives and backup tapes with sensitive data. Not for SSDs. |
| Shredding | Absolute | No | End-of-life drives, SSDs, or any media containing highly critical data. |
Selecting the right tool for the job ensures you achieve the optimal balance of security, cost-efficiency, and sustainability for every piece of hardware you retire.
The Smartest Strategy Is a Blended One
A sophisticated and cost-effective data destruction policy for Georgia enterprises often involves a blended approach. You don't have to choose only one method for all assets.
A blended strategy is often the most effective. Use certified wiping to recover value from newer assets and employ on-site shredding for older drives or those containing your company’s crown jewels. This perfectly balances security, cost, and sustainability.
For instance, a fleet of three-year-old laptops is an ideal candidate for data wiping and resale. However, the servers from a decommissioned data center that processed customer financial information should be designated for the shredder without question.
By matching the method to the asset, you guarantee absolute security where it is most critical while maximizing the financial return on your retired IT hardware. Explore our secure data destruction services to learn how we integrate these options into a complete security framework.
Meeting Data Security and Environmental Regulations in Georgia
When Georgia businesses retire IT assets, they face a dual compliance challenge: ensuring complete data destruction and disposing of the physical hardware in an environmentally responsible manner. A comprehensive IT Asset Disposition (ITAD) strategy is designed to address both of these critical liabilities in a single, streamlined process.
Failure to meet these obligations can result in significant fines, legal action, and severe damage to your company's reputation. A certified ITAD partner is essential for navigating this complex regulatory landscape.
Georgia’s Data Security and Breach Notification Laws
While Georgia lacks a single comprehensive privacy law like some other states, the Georgia Personal Identity Protection Act (GPIPA) places a clear responsibility on businesses to protect sensitive information and respond quickly in the event of a breach.
The core of GPIPA is its breach notification requirement. If unencrypted personal data is compromised—such as a name combined with a Social Security number, driver's license number, or financial account number—the business must notify the affected Georgia residents "without unreasonable delay." A single improperly disposed-of hard drive could easily trigger a public incident response.
Navigating Key Federal Regulations
In addition to state law, Georgia businesses must comply with powerful federal regulations governing data management, particularly in sensitive industries. These laws carry substantial penalties for non-compliance.
- FTC Disposal Rule: This rule requires businesses to take "reasonable measures" to protect against unauthorized access to consumer information during its disposal, applying to data on hard drives, laptops, and all other electronic media.
- HIPAA (Health Insurance Portability and Accountability Act): For healthcare organizations and their business associates, HIPAA’s Security Rule mandates specific administrative, physical, and technical safeguards for protecting electronic health information, including strict protocols for its final destruction.
- GLBA (Gramm-Leach-Bliley Act): Financial institutions must adhere to the GLBA Safeguards Rule, which requires a written information security plan detailing how they protect clients' nonpublic personal information from creation through secure destruction.
For Georgia enterprises, compliance isn't about picking and choosing which rule to follow—it's about creating a single, unified policy that covers all of them. A single act of improper disposal can violate GPIPA, the FTC Disposal Rule, and an industry-specific law like HIPAA all at once.
The Other Side of Compliance: Environmental Responsibility
Once data has been securely destroyed, the physical hardware—shredded metal and plastic, old server chassis, and laptop components—becomes electronic waste (e-waste).
Although Georgia does not have a statewide law mandating e-waste recycling, federal and state environmental regulations still apply. Electronics often contain hazardous materials like lead and mercury, which are regulated under the Resource Conservation and Recovery Act (RCRA) and Georgia Environmental Protection Division (EPD) rules. These materials cannot be disposed of in standard municipal landfills.
This is where a certified ITAD partner is indispensable. A provider holding an R2v3 or e-Stewards certification guarantees that all e-waste is managed in an environmentally sound manner. They ensure hazardous materials are handled correctly and that recyclable commodities are returned to the manufacturing supply chain, closing the loop on your assets' lifecycle. Our guide to compliant IT disposal in Georgia provides more detail on navigating these state and federal requirements.
The Power of an Auditable Paper Trail
In the world of corporate compliance and governance, an undocumented action is considered an action that never occurred. The only way to prove your data was destroyed securely is by creating an unbroken, auditable paper trail, a process known as maintaining the Chain of Custody.
This documentation is not mere paperwork; it is your legal defense. A robust Chain of Custody chronologically documents every touchpoint for your IT assets, from the moment they leave your Georgia facility to their final, certified destruction.

From Your Doorstep to Final Destruction
The Chain of Custody is the official biography of your retired hard drive. A certified ITAD partner meticulously documents this journey, ensuring there are no gaps or unanswered questions. For any enterprise in Georgia seeking to demonstrate due diligence, this process is non-negotiable.
The process includes several critical stages:
Serialized Asset Reporting: A detailed inventory is created before any assets are moved. Every device—server, laptop, or individual hard drive—is tagged with a unique serial number. This manifest serves as the foundation for the entire process.
Secure, GPS-Tracked Transportation: Assets are transported in locked, secure vehicles operated by vetted personnel. Real-time GPS tracking provides a complete log of the vehicle's journey from your location to the secure processing facility.
Access-Controlled Facilities: Upon arrival, equipment is received in a facility with strict access controls, 24/7 video surveillance, and monitored security systems, ensuring only authorized professionals handle your sensitive media.
This end-to-end tracking is the backbone of any trustworthy enterprise data destruction Georgia service. It transforms a simple equipment pickup into a verifiable security procedure. Organizing this paper trail can be simplified using efficient document management software.
Your Legal Shields: The Certificate of Destruction
The process culminates in the delivery of two of the most critical documents in IT asset disposition. These are not mere receipts; they are official legal records that formally transfer liability from your company to your destruction vendor.
A Certificate of Data Destruction is more than a formality—it is your definitive proof of compliance. This document allows you to confidently face internal audits, satisfy regulatory inquiries, and provide your leadership team with absolute peace of mind.
The key documents you must obtain and retain are:
- Certificate of Data Destruction: This document certifies that all data on the listed assets has been destroyed in accordance with specific standards (e.g., NIST 800-88 compliant shredding). It must include serial numbers, the date of destruction, and the exact method used. You can review a professional destruction certificate template to understand all the required components.
- Certificate of Recycling: Following destruction, this certificate confirms that the resulting electronic scrap was processed in an environmentally compliant manner, adhering to EPA regulations and certifications like R2v3.
Together, these documents create an irrefutable record demonstrating that you have fulfilled both your data security and environmental obligations. This documented proof is your ultimate protection against future liability.
How to Select Your Georgia ITAD Partner
Choosing the right partner for enterprise data destruction in Georgia is as critical as selecting the destruction method itself. The vendor you entrust with your retired IT assets becomes an extension of your security and compliance team. A true partner mitigates risk, whereas a simple scrap hauler can expose your organization to significant data and environmental liabilities.
Making an informed decision requires looking beyond the price quote to evaluate a potential partner's certifications, security protocols, and operational capabilities within Georgia.
The Non-Negotiables: Core Certifications
Certifications provide independent, third-party validation that a vendor adheres to strict industry standards for security, environmental responsibility, and operational transparency. For businesses in Georgia, two certifications are paramount:
- R2v3 (Responsible Recycling): This is the leading standard for electronics recycling, guaranteeing that e-waste is managed in an environmentally safe manner, data is handled securely, and worker health and safety are protected.
- e-Stewards: Another highly respected certification, e-Stewards places a strong emphasis on preventing the export of hazardous e-waste to developing nations and ensures the highest level of environmental and social responsibility.
A vendor operating without one of these certifications is working without proven accountability, placing your organization at risk.
On-Site vs. Off-Site Capabilities
Your specific security requirements should dictate where data destruction occurs. A qualified ITAD partner will offer both options, allowing you to align the service with your data's sensitivity.
- On-Site Destruction: A mobile shredding truck comes directly to your Georgia office, data center, or warehouse. You can witness the physical destruction of your hard drives and SSDs, eliminating any chain of custody risk during transport. This is the optimal choice for your most sensitive data.
- Off-Site Destruction: Your assets are securely transported to the vendor's facility for destruction. This requires a partner with GPS-tracked vehicles, fully vetted drivers, and a secure, access-controlled plant.
A flexible partner should accommodate your needs, whether it's on-site shredding in downtown Atlanta or a secure pickup from a facility in Augusta.
Vetting Security Protocols from End to End
A trustworthy partner will have robust, verifiable security measures in place. When evaluating a vendor for enterprise data destruction in Georgia, ask detailed questions about their security infrastructure.
The quality of a vendor's security protocols for their facilities and vehicles is a direct reflection of how seriously they will take the security of your data. Never settle for vague answers; demand specific, verifiable details.
Key security elements to inquire about include:
- Facility Security: Are their buildings monitored 24/7 with video surveillance? Is access controlled by keycards or biometrics? Are data-bearing assets stored in a locked, secure area upon arrival?
- Vehicle Security: Are trucks locked and sealed during transit? Do they have GPS tracking? Are drivers background-checked and trained in security protocols?
- Reporting and Documentation: Will they provide a complete, serialized report of every asset? Is their Certificate of Destruction sufficiently detailed to be legally defensible?
The Importance of a Local Georgia Presence
While national providers exist, selecting a vendor with a physical footprint in Georgia offers distinct advantages. A local partner can provide faster service, lower transportation costs, and more flexible scheduling.
More importantly, a local facility allows you to conduct your own audits and witness the destruction process firsthand. This transparency provides a level of assurance that cannot be replicated remotely. As you consider your options, remember the value of working with a partner who knows the local market. Learn more about selecting the right local vendor in our guide to ITAD services in Georgia.
Uncovering the Financial Value in IT Asset Disposition
Georgia businesses often view the disposal of old IT equipment as a cost center. However, a strategic IT Asset Disposition (ITAD) program can generate a positive return on investment. While enterprise data destruction is mandatory for any device containing sensitive data, not all retired assets must become scrap. Equipment like monitors, networking gear, or professionally wiped servers often retain significant resale value.
This is where IT asset value recovery can directly impact your budget.

How IT Asset Buyback Programs Work
An IT asset buyback program functions like a corporate technology trade-in. A certified ITAD partner like Beyond Surplus assesses your entire inventory of retired equipment. Assets that are still functional and have value on the secondary market can be purchased directly from your company.
The process is straightforward:
- Assessment: We evaluate the make, model, age, and condition of your hardware.
- Secure Sanitization: For any data-bearing devices, we perform certified data wiping according to NIST 800-88 standards, ensuring they are safe for resale.
- Fair Market Offer: You receive a transparent, fair market offer based on the current value of the hardware.
Revenue generated from a buyback program can offset or even exceed the cost of recycling and destroying non-functional or high-risk assets.
The Hidden Costs of Improper Disposal
Forgoing a professional ITAD program may appear cheaper initially, but it is a gamble with potentially catastrophic hidden costs. These liabilities often remain invisible until a security incident occurs.
The greatest financial risk isn't the cost of a shredder; it's the cost of a data breach. Framing professional ITAD as a strategic financial decision helps demonstrate how protecting company data also contributes directly to the balance sheet.
Consider the two potential paths. One leads to a process that can recover revenue for your business. The other exposes you to:
- Data Breach Fines: Regulatory penalties can reach millions of dollars.
- Reputational Damage: The long-term loss of customer trust can be financially devastating.
- Legal Fees: Defending your company after a breach is an expensive and resource-intensive process.
As Georgia's technology sector continues to expand, so does the economic value embedded within its hardware. When you partner with a certified provider for enterprise data destruction in Georgia, you are not just fulfilling a compliance requirement—you are making a prudent financial decision that protects your company's data, its reputation, and its bottom line.
Common Questions About Data Destruction in Georgia
After understanding the regulations and methods, practical questions often arise. We understand that before committing to an ITAD plan for your company's technology, you need complete clarity on the operational details.
Here are answers to some of the most common questions we receive from businesses across Georgia. Clear, direct answers are essential for launching your enterprise data destruction Georgia program with confidence.
Can You Perform Hard Drive Shredding at Our Office in Georgia?
Yes, absolutely. On-site shredding is one of our most requested services for companies requiring maximum transparency and security. We dispatch our mobile shredding truck directly to your location, whether you are in Atlanta, Alpharetta, Savannah, or Augusta.
The primary benefit of on-site service is the complete elimination of chain-of-custody risks associated with transporting data-bearing drives. Your team can witness the entire destruction process, providing visual confirmation that every hard drive, SSD, and backup tape is destroyed before our truck leaves your premises. A Certificate of Destruction is provided upon completion of the job.
What Happens to the Shredded Materials After Destruction?
This is a critical question that addresses environmental responsibility. After your drives are shredded into fragments, the mixture of metal and plastic is securely transported from your Georgia facility to one of our certified recycling partners.
There, the material undergoes advanced separation processes. Commodities like aluminum and steel are sorted, refined, and reintroduced into the manufacturing supply chain for use in new products. This two-step process guarantees that 100% of your data is unrecoverable and that all resulting e-waste is managed in a compliant and environmentally sustainable manner.
Is Data Wiping Secure Enough for Our Company's Sensitive Data?
Yes, for many use cases, certified data wiping is an exceptionally secure and often more cost-effective option. When performed according to a strict standard like NIST 800-88, the wiping software overwrites the drive's data multiple times, making the original information forensically unrecoverable.
Wiping is the ideal solution for newer, functional equipment intended for resale or internal redeployment, as it allows for value recovery. However, for drives that contained your most critical intellectual property, or if your internal security policy mandates it, nothing provides greater assurance than physical shredding. A blended approach often works best for most businesses.
What Kind of Documentation Will We Receive for Our Records?
You will receive a complete, audit-ready documentation package that serves as your legal proof of compliant disposal. This paperwork is essential for internal audits, regulatory inquiries, and demonstrating due diligence.
Every project includes:
- A serialized inventory of every asset processed.
- A formal Certificate of Data Destruction, which details the destruction method, date, and confirms compliance with relevant standards.
- A Certificate of Recycling to verify that all physical components were recycled in an environmentally responsible manner.
This documentation creates an unbroken paper trail, formally transferring the liability for the retired assets from your company to ours.
For a partner that provides clear answers and certified, secure solutions, contact Beyond Surplus for all your electronics recycling and enterprise data destruction needs in Georgia. Visit us at https://technostolic.com to schedule your service.