Old laptops in a closet, decommissioned servers on a pallet, retired network switches under a workbench. That’s how ewaste recycling usually starts inside a business. Not with a sustainability initiative, but with a space problem, a refresh cycle, an office move, or a data center cleanup.
The mistake is treating that pile as junk. It isn’t. It’s a mix of regulated data risk, environmental liability, and recoverable asset value. If your team handles disposal casually, you can lose control of drives, serial-numbered assets, and downstream accountability in one move.
The Hidden Risks in Your Old IT Equipment
Most organizations keep obsolete equipment longer than they should. The usual reason is uncertainty. Someone knows there’s still data on the devices. Someone else thinks some of it may have resale value. Procurement wants it off the books. Compliance wants documentation. So the equipment sits.

That delay creates its own risk. Drives go missing. Asset records drift from reality. Business units dispose of items outside approved channels. The result is exactly the kind of exposure described in this overview of data breaches from improper equipment disposal.
Why old equipment is still an active risk
Retired hardware often contains more than files. It may hold customer records, employee data, credentials, cached email, device configurations, licensed software, or regulated health and financial information.
A copier hard drive, a firewall, or an old SAN can be more sensitive than a laptop. Many companies focus only on desktops and miss the infrastructure layer entirely.
Practical rule: If a device stored data, processed data, or touched your network, handle it like a security asset until proven otherwise.
The business problem is larger than one storeroom
The global waste stream makes the urgency hard to ignore. In 2022, global e-waste generation reached a record 62 million tonnes, an 82% increase from 2010. Only 22.3% was formally collected and recycled, leaving over 48 million tonnes undocumented according to the World Health Organization fact sheet on electronic waste).
For an enterprise, that translates into three practical questions:
- Who controlled the assets: Was there documented custody from removal through final disposition?
- How was data destroyed: Was media wiped, shredded, or both, and can the vendor prove it?
- What value was preserved: Were reusable assets remarketed before they were destroyed for scrap?
A mature ITAD program answers all three. That’s what separates strategic ewaste recycling from a truck pickup.
What Qualifies as Business E-Waste
Most buyers start with laptops, desktops, and monitors. That’s only part of the inventory. In practice, business e-waste includes nearly every retired electronic asset in your workplace, warehouse, clinic, branch location, and data center.
Core IT equipment
This is the obvious category, but it still needs disciplined scoping.
- User devices including laptops, desktops, thin clients, tablets, and mobile phones
- Peripherals such as docks, keyboards, mice, webcams, and external drives
- Print environment assets including printers, MFPs, scanners, and label systems
These items move fast during refresh cycles. They also spread across many departments, which makes chain-of-custody harder if the project is loosely managed.
Data center and infrastructure gear
This category is where many disposal plans break down. Infrastructure equipment is bulkier, harder to uninstall, and more likely to contain embedded storage.
Common infrastructure assets
- Rack servers
- Blade systems
- Storage arrays
- Backup appliances
- UPS units
- PDUs
- KVM hardware
- Tape libraries
Networking equipment belongs here too, even when teams don’t think of it as ewaste recycling.
- Routing and switching gear often retains configs, credentials, and topology data.
- Security appliances may store logs, policies, and sensitive network details.
- Wireless hardware still requires inventory control and documented disposition.
Specialized commercial equipment
Business ewaste isn’t limited to IT departments. Other functions generate high-risk electronics that need the same discipline.
Regulated and operational assets
- Medical devices with digital storage
- Laboratory analyzers and related electronics
- Industrial control interfaces
- POS systems
- VOIP phones and conferencing gear
- Digital signage and A/V equipment
In healthcare and research settings, the issue isn’t just recycling. It’s whether the organization can prove secure handling of every serialized device.
A good inventory review usually expands the project scope. Once teams look beyond “old computers,” they find gear in clinics, test labs, branch offices, storage rooms, and IDF closets.
Items businesses often overlook
The missed assets are predictable. External backup drives. Failed SSDs. Loaner laptops. Conference room systems. Retired access control panels. Broken handheld scanners. Demo units in marketing storage.
If it has a board, drive, battery, display, or power supply, it belongs in the conversation. The operational goal is simple. Build one disposition stream for all retired electronics, then sort by data risk, reuse potential, and recycling path.
The Secure IT Asset Disposition Lifecycle
Professional ewaste recycling works like a secure supply chain in reverse. Instead of receiving, deploying, and tracking assets into service, you’re collecting, documenting, sanitizing, and routing them out of service without losing control.
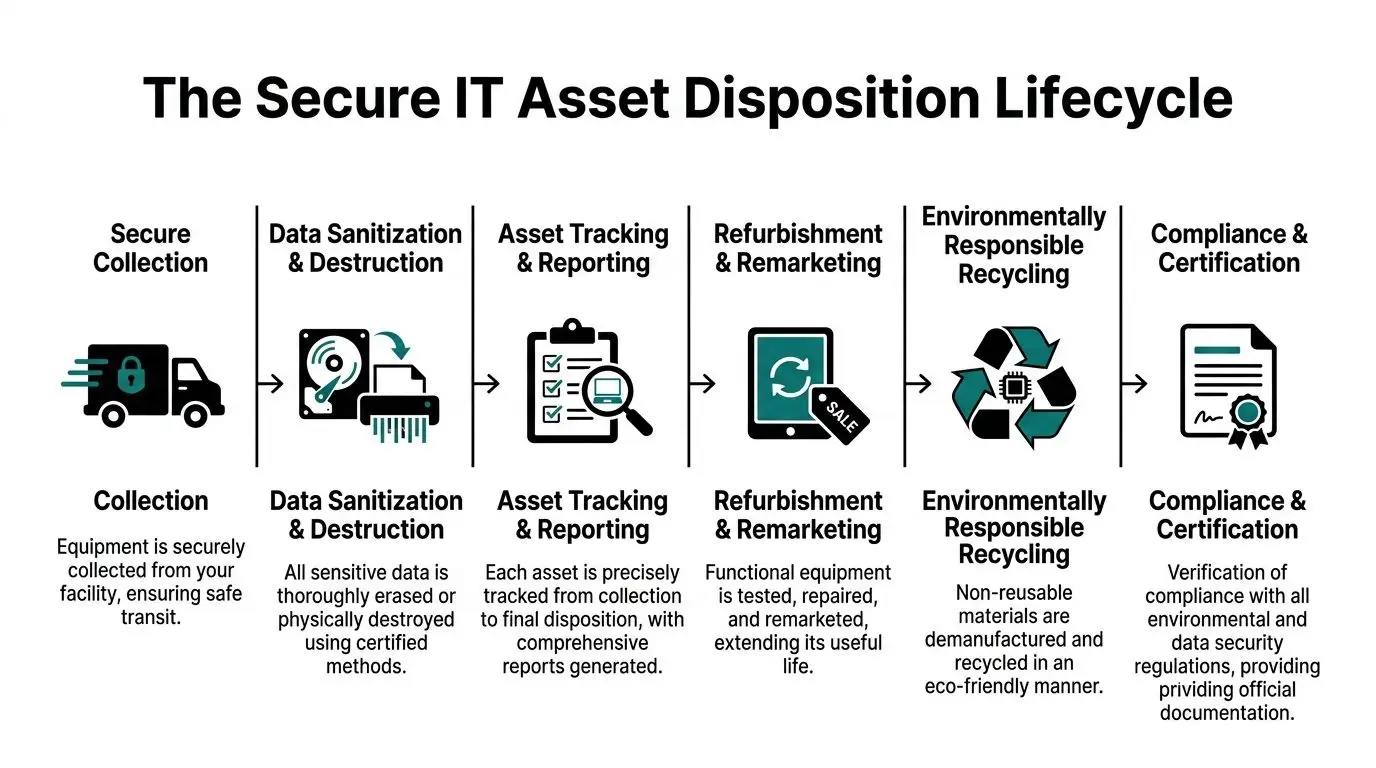
Secure collection and controlled logistics
The process starts before the truck arrives. Your vendor should define pickup scope, packaging method, site contacts, loading responsibilities, and custody transfer points.
For multi-site projects, logistics discipline matters as much as recycling capability. That’s one reason IT leaders often align disposition with broader asset lifecycle management practices. End-of-life control is part of the lifecycle, not a separate afterthought.
What works:
- Scheduled pickups tied to site readiness
- Sealed gaylords, pallets, or locked containers where appropriate
- Pickup manifests matched to internal asset records
What doesn’t:
- Ad hoc cleanouts with no pre-count
- Mixed loads from multiple departments with no owner
- Unlabeled loose drives and accessories
Inventory and audit
Once equipment enters the stream, every serious provider audits it. That means model identification, condition review, and serial capture when applicable. This makes the project defensible.
What the audit should establish
- Which assets were received
- Which assets contained data-bearing media
- Which units are candidates for reuse
- Which items require destruction or commodity recycling
For organizations formalizing this process, the service model behind IT asset lifecycle management usually combines inventory control, data handling, and disposition reporting under one chain of accountability.
Data sanitization and destruction
This is the highest-stakes step. Some assets can be wiped and redeployed or resold. Others should be physically destroyed because the media is failed, encrypted without key control, damaged, or too sensitive for reuse.
There isn’t one universal answer.
- Software wiping fits reusable devices when the media is functional and the sanitization standard is documented.
- Physical shredding fits failed drives, high-sensitivity media, and organizations that want definitive destruction.
- Hybrid workflows are common. Reuse what can be safely sanitized. Destroy what cannot.
If a vendor can’t explain when they wipe and when they shred, they probably don’t have a mature process.
Refurbishment before recycling
The best value recovery happens before shredding. Functional laptops, current-generation servers, and usable network gear may retain remarketing value if they’re tested, graded, and processed correctly.
That requires triage. Some equipment belongs in secondary markets. Some belongs in donation or redistribution programs. Some is only suitable for parts harvesting. The wrong decision destroys value fast.
Material processing and downstream recycling
After reusable equipment is removed, the remainder enters demanufacturing and recycling. Certified processors use staged methods such as shredding, magnetic separation, and hydrometallurgy. Formal recycling of 13.8 million tonnes of e-waste in 2022 prevented 93 million tonnes of CO2-equivalent emissions, and certified processes use multi-stage techniques to achieve over 95% recovery for key metals according to this technical overview of global e-waste statistics and recycling methods.
That matters for business clients because downstream quality determines whether your vendor is recycling responsibly or moving risk elsewhere.
Navigating Critical Compliance and Regulations
Companies don’t get in trouble because they intended to recycle. They get in trouble because they can’t prove secure handling, lawful disposal, and appropriate data destruction.
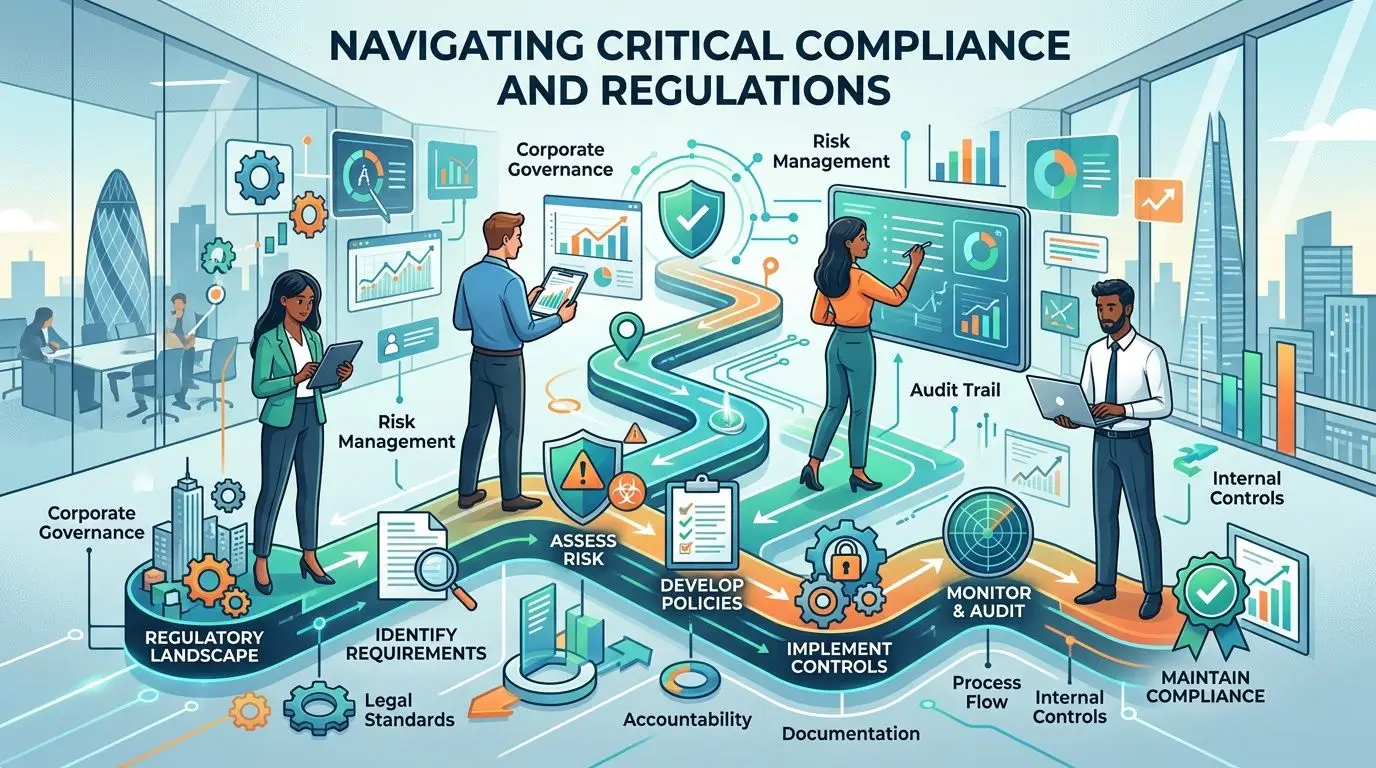
Why compliance drives the whole process
Ewaste recycling for business assets is a compliance exercise with environmental outcomes, not the other way around. The first question is whether retired equipment contains regulated or confidential data. The second is whether your organization can document what happened to it.
A primary barrier to recycling is fear of data breaches and compliance failures. That concern is grounded in reality. An estimated 80-85% of US e-waste is landfilled or unaccounted for, which is why documented ITAD processes matter, as noted in this analysis of barriers to e-waste recycling and liability transfer.
The rules that affect disposal decisions
Different sectors feel this differently.
- FTC Disposal Rule applies when customer report information is involved. Disposal has to be reasonable and appropriate.
- HIPAA affects healthcare organizations that retire devices containing protected health information.
- State e-waste laws add disposal and handling requirements that vary by location.
- Contractual obligations often go further than regulation, especially in finance, government, and enterprise outsourcing environments.
The practical burden falls on the generator of the equipment. If your company owned the assets, your company needs a defensible process.
What auditors and legal teams care about
Auditors rarely start with the recycler’s marketing language. They ask for evidence.
They will want to see
- Asset lists and pickup records
- Chain-of-custody documentation
- Data destruction records
- Recycling or final disposition certificates
- Policies tied to recognized sanitization standards, such as NIST SP 800-88
Compliance fails most often in the handoff. Internal teams approve disposal, but no one verifies custody, media handling, or final documentation.
This is why “free pickup” by an unknown hauler is usually a bad idea for enterprise equipment. If the provider can’t support legal review, procurement due diligence, and audit requests, the low upfront price isn’t savings. It’s risk.
Proof of Compliance The Role of Certificates
A truck receipt is not proof of secure disposal. It proves only that someone removed equipment from your site. Compliance depends on what happened after that.
What the right certificates do
Two documents carry the most weight.
The first is a Certificate of Data Destruction. It confirms that media was sanitized or physically destroyed according to the agreed method. The second is a Certificate of Recycling. It confirms that non-reusable material entered an approved recycling stream rather than landfill or uncontrolled export. A credible vendor should support both with serialized reporting where applicable. That’s what turns a certificate from a generic form into evidence.
Chain-of-custody is the primary control point
Certificates matter because they sit at the end of a documented chain. Without custody records, even a polished certificate is weak.
A strong chain-of-custody file typically includes:
- Pickup details showing date, location, and authorized release
- Asset identification with serial numbers or itemized lot descriptions
- Processing records tied to wiping, shredding, refurbishment, or recycling
- Final documents matching the scope of assets received
Many providers separate themselves here. Some issue broad summary paperwork. Others provide documentation that legal, compliance, and internal audit teams can use. A sample certificate of destruction is useful because it shows the level of detail you should expect before signing a service agreement.
Good documentation doesn’t just support sustainability reporting. It transfers operational liability by showing who had custody, what method was used, and when final disposition occurred.
What to reject
A weak paperwork package usually has obvious gaps.
- No reference to sanitization method
- No reconciliation to pickup inventory
- No distinction between reused and destroyed assets
- No sign of downstream accountability
- No named contact who can answer audit questions later
If your organization operates in healthcare, finance, government, or any regulated environment, documentation should be reviewed before the first pickup, not after.
Maximizing Value Recovery from Retired IT Assets
Most organizations think of ewaste recycling as a disposal cost center. That’s incomplete. The better model is value recovery after risk control.
Reuse creates the highest return
Commodity recycling has a place, but reuse usually returns more value than shredding material for metals and plastics. That means testing devices early, separating functional assets from scrap, and preserving configurations that affect resale.
The assets most likely to retain value are usually:
- Recent business laptops
- Enterprise servers still relevant in secondary markets
- Network gear with demand in refurbishment channels
- Bulk lots of standardized equipment with clean asset records
The opposite is also true. Missing power supplies, broken screens, poor packing, and mixed unsorted loads reduce recovery.
Donation and redistribution can serve two goals
Not every reusable asset should be sold. Some equipment is better suited to refurbishment and redistribution. Global e-waste contained $62.5B in metals in 2022, but refurbishment programs also create social ROI and may provide tax benefits according to the World Economic Forum’s overview of ewaste recycling and redistribution.
That matters for corporate programs with ESG, community investment, or digital access goals. A redeployed device can generate value in more than one form.
The financial equation is broader than resale
The full business case includes avoided costs, not just recovered dollars.
Consider the value streams:
- Direct recovery from resale or buyback
- Commodity value from responsibly recycled material
- Avoided storage cost from clearing obsolete inventory
- Avoided incident cost from preventing data exposure
- Program value from donation, tax treatment, and sustainability reporting
A practical ITAD strategy doesn’t maximize one line item in isolation. It balances resale, destruction, compliance, and operational simplicity. The wrong choice is often destroying everything for speed. The second wrong choice is trying to sell everything and delaying secure processing.
How to Select a Certified E-Waste Recycling Partner
Vendor selection should look more like security due diligence than junk removal. You’re choosing a custodian for retired assets, data-bearing media, and audit evidence.
What to ask before you sign
Start with operating details, not branding.
- Security controls matter. Ask who can access the facility, how media is segregated, and how visitors are handled.
- Data destruction options should be clear. Can they support on-site shredding, off-site shredding, and wiping workflows?
- Logistics capability should match your footprint. Multi-site pickups, packing support, and de-install labor are different services.
- Downstream transparency matters. Ask how they manage non-reusable fractions after initial processing.
Technology is a useful differentiator. Advanced automated recycling using robotics and AI-powered sorting can achieve up to 98% purity in extracting precious metals and can run 5x faster than manual dismantling, which affects recovery value and processing quality, as described in this article on innovations in recycling processes.
ITAD provider vetting checklist
| Evaluation Criteria | What to Verify | Importance |
|---|---|---|
| Certifications | Confirm current R2, e-Stewards, or equivalent claims | Shows process discipline and downstream expectations |
| Data destruction | Verify wiping standards, shredding options, and reporting format | Protects regulated and confidential data |
| Chain-of-custody | Review manifests, serialized reports, and final certificates | Supports audits and liability transfer |
| Logistics | Check pickup coverage, site labor, and packaging requirements | Prevents custody gaps during collection |
| Value recovery | Ask how reuse, buyback, and commodity recovery are separated | Preserves asset value before scrap |
| Downstream controls | Confirm how materials move after initial processing | Reduces environmental and reputational risk |
| Insurance and legal readiness | Request proof of coverage and contract terms | Helps procurement and legal review |
A formal vendor due diligence checklist is worth using because it forces apples-to-apples comparison across providers.
Choose the vendor whose process your compliance officer can defend, your security team can trust, and your finance team can reconcile.
For organizations that need nationwide pickups, on- or off-site drive destruction, certificates of recycling and destruction, and IT buyback support, Beyond Surplus is one example of an ITAD provider that offers those services for business clients.
If your company is sitting on retired laptops, servers, networking gear, medical devices, or mixed electronic surplus, contact Beyond Surplus for certified ewaste recycling, secure IT asset disposal, and documented chain-of-custody support that helps reduce risk, support compliance, and recover value from end-of-life technology.