Effective IT asset removal is far more than just unplugging obsolete equipment. For businesses across the United States, it's a critical operational process that safeguards sensitive data, maximizes value from retired hardware, and ensures compliance with stringent environmental and legal regulations. A successful IT asset removal project for any commercial enterprise hinges on meticulous planning, certified data destruction, and a transparent, auditable process from collection to final disposition.
Building Your IT Asset Removal Game Plan

Before a single server is powered down or a laptop is boxed up, every successful asset removal project begins with a comprehensive strategy. This is not a simple cleanup task but a proactive measure to mitigate risk, enhance financial returns, and protect your company’s reputation. This plan serves as the definitive roadmap for the entire IT asset disposal journey, a critical service for businesses throughout the United States.
Market data underscores this necessity. The global IT asset disposition (ITAD) market was valued at USD 17.5 billion in 2025 and is projected to reach USD 40.1 billion by 2035, expanding at a robust CAGR of 8.9%. This growth is driven by enterprise-level technology upgrades and the large-scale retirement of legacy equipment. North America leads this trend, with the U.S. market alone expected to hit USD 5.3 billion in 2025, fueled by strict compliance demands in sectors like healthcare, finance, and government.
Assembling Your Cross-Functional Team
A common pitfall for businesses is treating IT asset removal as an isolated IT function. In reality, a seamless project requires expertise and collaboration from multiple departments to ensure all corporate responsibilities are met.
Your core team should include:
- IT Department: Manages the technical aspects, including creating the asset inventory, identifying specific equipment for disposal, and overseeing the physical decommissioning of hardware.
- Finance Department: Focuses on financial considerations, such as asset depreciation, maximizing value recovery through equipment resale, and maintaining budget oversight. They are essential for transforming this process from a cost center into a potential revenue source.
- Legal and Compliance: Ensures every step aligns with data privacy laws (e.g., FTC Disposal Rule, HIPAA), environmental regulations, and internal corporate policies.
- Facilities Management: Coordinates the physical logistics, including scheduling building access for the removal team, managing power shutdowns, and ensuring a safe workspace during the project.
Engaging these stakeholders from the outset helps identify potential challenges and align on objectives before they escalate. To understand the broader context, review the fundamentals of IT Asset Disposition.
Defining a Clear Project Scope and Timeline
Without a clearly defined scope, an IT asset removal project can easily exceed its budget and timeline. The project scope must explicitly detail what is included—and what is excluded.
For instance, a laptop refresh project for a United States-based enterprise would specify the models being retired, the office locations for collection, and the final deadline. In contrast, a data center decommissioning involves a much more complex scope, encompassing servers, networking gear, storage arrays, and power distribution units.
A well-defined scope statement is the best defense against "scope creep." It should explicitly list the assets for removal, physical locations, required data destruction standards, and key deliverables like certificates of destruction and recycling.
Once the scope is established, a realistic timeline with clear milestones is essential.
IT Asset Removal Planning Checklist
This table outlines the essential phases for creating your IT asset removal plan.
| Planning Phase | Key Objective | Core Activities |
|---|---|---|
| Initial Assessment | Understand the project's scale and requirements. | Identify stakeholders, define high-level goals, and estimate asset volume. |
| Scope Definition | Create a precise and agreed-upon project boundary. | List specific assets, locations, and services required (e.g., data wiping, recycling). |
| Team Assembly | Bring together a cross-functional group. | Assign roles from IT, Finance, Legal, and Facilities. Schedule a kickoff meeting. |
| Timeline & Budget | Establish clear deadlines and financial constraints. | Set key milestones, allocate funds, and get budget approval. |
| Partner Selection | Choose a certified and reliable ITAD vendor. | Vet potential partners, check certifications (R2, e-Stewards), and request quotes. |
This structured approach transforms a potentially chaotic process into a predictable and manageable business operation.
Creating An Ironclad Asset Inventory
With your strategy in place, the next critical step is building a meticulous inventory. This is more than a simple list; it is the foundational document for your entire it asset removal project. Without accurate tracking, businesses risk security gaps, compliance violations, and a broken chain of custody.
This inventory serves as the master ledger for every retired device, acting as the single source of truth for all subsequent steps, from data destruction to logistics and final reporting. An inaccurate inventory is a direct path to lost assets and significant data vulnerabilities.
Capturing Essential Asset Details
To ensure accuracy, specific data points must be captured for each piece of equipment. This level of detail is non-negotiable for tracking, valuation, and accountability.
Your inventory system should include fields for:
- Unique Asset Tag: Your company’s internal ID number.
- Serial Number: The manufacturer’s unique identifier.
- Make and Model: Specifics like "Dell Latitude 7420" or "HPE ProLiant DL380 Gen10."
- Asset Type: Categories such as Laptop, Server, Switch, or Monitor.
- Physical Location: The building, floor, and room where the asset is located before removal.
This granularity eliminates ambiguity when the removal team arrives, enabling a one-to-one reconciliation between your records and the physical hardware. For more on this, our guide on IT asset management best practices offers valuable insights.
Choosing Your Inventory Method
The appropriate tool depends on the project's scale. A small office retiring a few devices has different needs than a large enterprise decommissioning an entire data center.
- Spreadsheets (For Smaller Projects): For simple removals, a well-organized spreadsheet can suffice. It's cost-effective and easy to share but relies on manual entry, increasing the risk of human error with larger asset counts.
- Asset Management Software (For Larger Projects): For projects involving hundreds or thousands of assets, dedicated IT Asset Management (ITAM) software is essential. These platforms often use barcode scanners, automate data entry, and generate audit-ready reports.
The need for a professional approach is clear. Large enterprises accounted for 66.9% of the ITAD market share in 2025, driven by the complexity of their disposal projects. Globally, 61.9 million metric tonnes of e-waste were generated in 2022, with only 22.3% properly recycled.
Key Takeaway: Your inventory is the backbone of your chain of custody. It is the document that proves every asset was securely handled, every hard drive was destroyed, and all e-waste was responsibly recycled.
Ultimately, this detailed record provides verifiable proof for any audit, serving as your first line of defense against inquiries about data security and environmental compliance.
Choosing The Right Data Destruction Method
Your responsibility for data security persists long after a device is powered down. This is when its stored data is most vulnerable. A casual approach to data disposal can undermine years of security protocols, exposing your business to breaches and significant regulatory penalties. Selecting the right data destruction method is a mandatory component of a secure IT asset removal process.
The optimal method depends on the storage media type, your industry's compliance requirements, and whether you intend to recover value from the asset. The primary goal is to render the data completely irrecoverable, ensuring sensitive information never falls into unauthorized hands.
This decision tree provides a visual guide to help select the right method for your specific storage device.
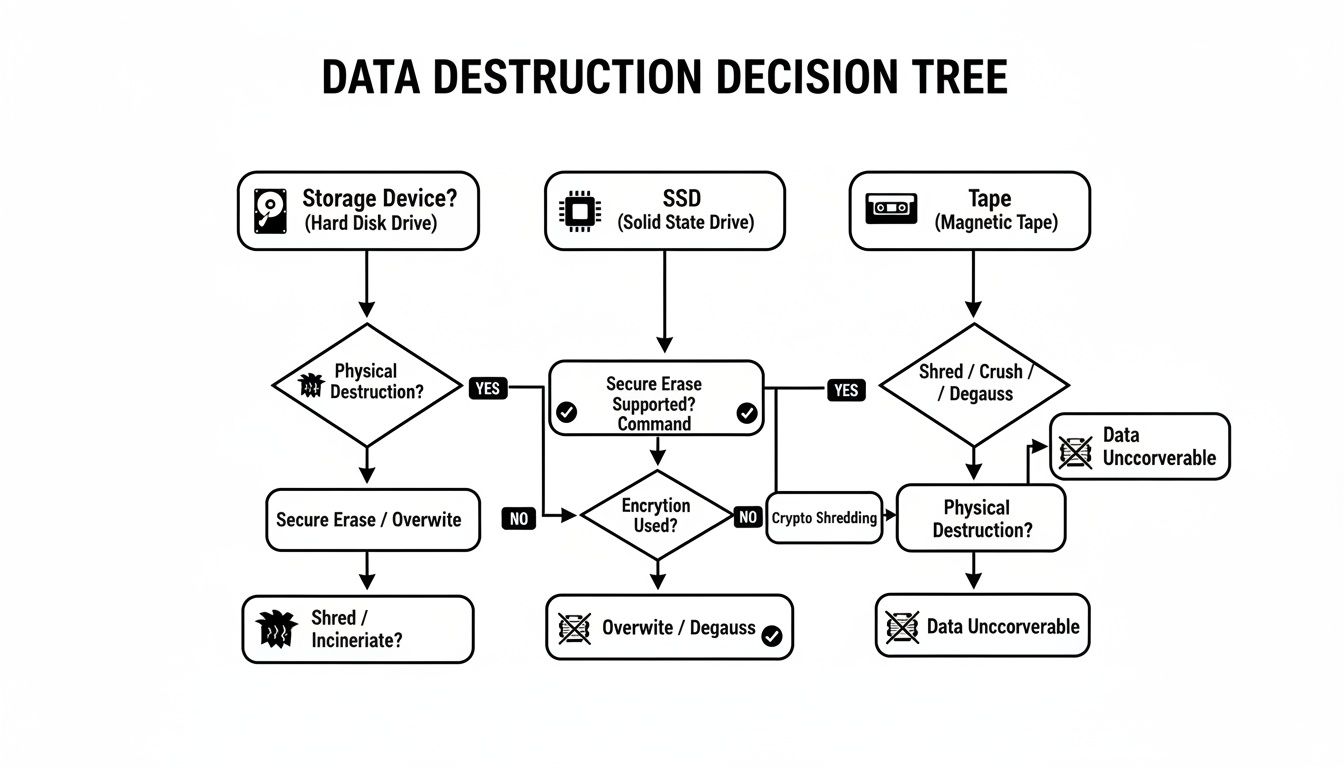
The underlying technology—whether magnetic platters in an HDD, flash memory in an SSD, or magnetic tape—determines the most effective sanitization technique.
Certified Data Wiping for Asset Reuse
Data wiping, or sanitization, uses specialized software to overwrite all existing data with random characters. This is the preferred method when you want to preserve the physical asset for resale or internal redeployment.
Its key advantage is its ability to meet stringent standards like the NIST 800-88 guidelines, a common requirement for regulatory compliance. When performed by a certified partner, wiping makes the original data unrecoverable while leaving the drive functional. This maximizes the financial return on your IT assets without compromising security.
However, not all drives can be wiped. If a drive is failing or physically damaged, the wiping process may not complete successfully. For such assets, physical destruction is the only secure option.
Physical Destruction for End-of-Life Media
When an asset has no resale value or its storage media cannot be reliably wiped, physical destruction is the definitive solution. This requires industrial-grade equipment to guarantee complete data obliteration.
The primary methods include:
- Degaussing: This technique exposes hard disk drives (HDDs) and magnetic tapes to a powerful magnetic field, instantly scrambling the data. It is fast and effective for magnetic media but completely ineffective on solid-state drives (SSDs).
- Shredding: This is the most secure and foolproof method. Industrial shredders grind hard drives, SSDs, smartphones, and other devices into small, irrecoverable fragments, making data recovery impossible.
Demand for these services is significant. Data destruction services constituted the largest segment of the ITAD market, valued at USD 5 billion in 2025, highlighting its importance for businesses mitigating data breach risks.
Comparison of Data Destruction Methods
| Method | Best For | Compliance Level | Asset Reuse Potential |
|---|---|---|---|
| Data Wiping | Functional HDDs and SSDs intended for resale or redeployment. | High (Meets NIST 800-88, DOD 5220.22-M) | Excellent – Preserves the hardware. |
| Degaussing | End-of-life HDDs and magnetic tapes. Not effective for SSDs. | Very High (Meets NSA requirements) | None – Renders the drive inoperable. |
| Shredding | All media types, including damaged drives, SSDs, and phones. | Absolute – The highest level of security. | None – Physically destroys the asset. |
The choice depends on balancing security needs with asset value recovery potential.
On-Site vs. Off-Site Destruction
The location of data destruction is another key decision. Both on-site and off-site services offer different balances of security, convenience, and cost.
- On-Site Destruction: A mobile shredding truck or data wiping station comes to your facility. This offers maximum security, as your team can witness the process, maintaining a perfect chain of custody. It is standard for highly regulated industries.
- Off-Site Destruction: Assets are transported in locked, secure containers to a certified facility. This is often more cost-effective for large volumes of equipment. A reliable partner will provide a complete chain-of-custody record from pickup to destruction.
Regardless of the chosen method, the process is incomplete without a Certificate of Data Destruction. This legal document is your official proof of due diligence, listing the serial numbers of all media destroyed and formally transferring liability to the vendor.
This certificate is your primary defense in an audit, proving you took all necessary steps to protect your data. Explore our complete guide on secure data destruction services for more details.
Securing Your Assets During Transport

The moment your IT assets leave your premises is the most vulnerable point in the it asset removal process. All prior inventory and data destruction efforts can be negated if equipment is lost, damaged, or stolen in transit.
This is why a robust chain of custody is non-negotiable. It is the documented, unbroken trail that tracks every asset from your facility to its final processing, forming the logistical backbone of your compliance strategy.
Establishing An Auditable Trail
An auditable trail begins the moment your ITAD partner arrives. Their first action should be to reconcile the physical equipment against your inventory list. Each pallet or container is scanned and documented before being loaded onto a locked, GPS-tracked vehicle.
This serialized tracking continues at every transfer point. Upon arrival at the processing facility, the shipment is inspected, and every asset is rescanned to confirm that what left your site is exactly what arrived. This creates a transparent record for internal audits and regulatory compliance.
A robust chain of custody provides irrefutable proof of secure handling. It should detail every individual who handled the assets, the time and date of each transfer, and all secure locations involved.
This documentation serves as proof that you fulfilled your duty of care, a critical element in demonstrating compliance with regulations like the FTC Disposal Rule.
Best Practices for Secure Logistics
Securely transporting your equipment requires a coordinated effort to mitigate risks. A professional ITAD provider will have a refined process.
Key elements include:
- Secure Packing: Sensitive equipment should be packed in sealed, tamper-evident containers. Opaque shrink-wrap is often used to conceal contents.
- Dedicated Transport: The vehicle used for pickup should be dedicated solely to your project, preventing mix-ups and minimizing stops.
- Vetted Personnel: All drivers and technicians must be background-checked and trained in secure logistics protocols.
- Real-Time Tracking: GPS tracking on all vehicles provides constant visibility of your shipment's location.
Coordinating Nationwide Pickups
For companies with multiple offices, data centers, or a remote workforce across the United States, logistics can become complex. A consistent process is needed to ensure security and compliance are uniformly applied everywhere.
This requires an ITAD partner with expertise in nationwide reverse logistics services. They possess the network to coordinate secure pickups from any location, applying the same strict chain-of-custody protocols regardless of the office's location. This centralized approach simplifies project management and provides a single, consolidated report.
By leveraging an expert partner, you can ensure your it asset removal is secure, efficient, and compliant, no matter how geographically dispersed your assets are.
Getting Paid for Old Tech and Doing Right by the Planet
That closet full of retired IT equipment doesn’t have to be a liability. With a smart IT asset removal plan, that old hardware can actually put money back in your budget and prove your company is serious about sustainability. This one-two punch of value recovery and environmental responsibility is what really separates a professional ITAD process from just hauling away junk.
The magic starts the moment your gear hits a certified facility. A good ITAD partner doesn’t just see a pallet of old computers; they see potential. Each and every device is carefully evaluated to see if it can be refurbished and find a new home on the secondary market.
How You Get a Return on Your Old Assets
The heart of the value recovery process is a detailed appraisal. It’s not guesswork. An ITAD specialist will size up each asset based on a few key factors to figure out what it's worth.
Here’s what they’re looking at to determine the buyback value:
- Age and Model: No surprise here—newer models fetch higher prices. A three-year-old enterprise laptop is going to be worth a lot more than a seven-year-old desktop.
- Condition: This is huge. They'll check both the cosmetic condition and whether it actually works. A device in good working order with just a few scuffs is a perfect candidate for remarketing.
- Specs: What’s under the hood matters. A server loaded with top-tier processors, maxed-out RAM, and big SSDs will bring in way more cash than a basic configuration.
- Market Demand: Like any market, this one has its ups and downs. A certain server model might be really hot for building home labs or for small businesses, which drives its price up.
Based on this deep dive, your ITAD partner makes you a fair market value offer. The money made from selling these refurbished assets comes right back to you, which can seriously offset—or even completely cover—the costs for data destruction and recycling.
And this isn't just pocket change. Value recovery is a massive part of the ITAD world, projected to make up 36.95% of the total market revenue in 2025. It’s proof that businesses can turn retired gear from a cost center into a real revenue stream. The server market is especially booming, with a projected 12% CAGR as data centers constantly refresh their hardware. You can dig into more of these trends in this full ITAD industry analysis.
The Non-Negotiable: Responsible E-Waste Recycling
Let's be realistic—not every piece of equipment is a winner. Older, broken, or just plain obsolete assets have reached the end of the line. This is where the next critical step kicks in: responsible e-waste recycling. Just tossing electronics into a dumpster isn't just bad for the planet; it can land your company in hot water with some serious legal and financial penalties.
Old electronics are full of nasty stuff like lead, mercury, and cadmium. If that gets into a landfill, those toxins can seep into the soil and groundwater, causing environmental damage that lasts for decades. This is why linking up with a certified e-waste recycler is a must-have for your corporate social responsibility (CSR) goals.
A certified recycler—someone who is R2 (Responsible Recycling) or e-Stewards compliant—is your guarantee that all those hazardous materials are handled safely. They also make sure valuable commodities like metals, plastics, and glass are recovered and put back into the manufacturing supply chain.
This approach ensures your end-of-life assets are taken apart in an environmentally sound way, preventing pollution and saving precious natural resources.
The final piece of the puzzle is the paperwork. Once everything is recycled, you should get a Certificate of Recycling. This is your official proof that your e-waste was handled according to all local, state, and federal environmental laws. It closes the loop on that asset’s life and gives you the auditable trail you need to show you’re committed to doing things the right way.
The physical work of an IT asset removal project might be done, but the job isn’t truly finished until you have the paperwork to prove it.
Honestly, this final documentation package is probably the most critical part of the whole process. It’s your official record of compliance and your shield against any future liability. Without it, you have no verifiable proof that your company’s data was secured or its e-waste was handled responsibly.
Think of these reports as your legal evidence. They confirm you met all your data security and environmental obligations, effectively transferring liability from your organization to your certified ITAD partner. This creates a defensible audit trail that keeps both internal governance and external regulators happy.
The Three Pillars of Compliant Documentation
A complete reporting package from any reputable ITAD vendor should always include three key documents. Each one serves a distinct but equally important purpose in closing out your project for good.
- Certificate of Data Destruction: This is the legal document confirming all your data-bearing devices were sanitized according to industry standards. It needs to detail the method used—like wiping to NIST 800-88 standards or physical shredding—and list the serial numbers of every single drive that was processed.
- Certificate of Recycling: For any assets that couldn't be resold, this document certifies they were processed in an environmentally compliant manner. It’s your proof that you followed all federal, state, and local e-waste regulations, keeping hazardous materials out of landfills.
- Serialized Audit Report: This is the master document that ties everything together. It should perfectly reconcile the initial inventory you created with the final outcome of every single asset, matching each serial number to whether it was remarketed, recycled, or destroyed.
Using Reports for Audits and Peace of Mind
This documentation is indispensable when it comes to internal audits. It allows you to demonstrate a clear, unbroken chain of custody to your leadership and compliance teams. It’s the concrete evidence you need to satisfy regulations like the FTC Disposal Rule, HIPAA, or strict financial services mandates.
The sheer volume of hardware being retired makes this documentation more important than ever. For instance, an estimated 240 million Windows 10 PCs are expected to be retired in 2025 alone as businesses upgrade. According to GMI Insights on ITAD market trends, this massive wave puts immense pressure on ITAD providers to deliver scalable, secure, and fully documented services.
Key Takeaway: Your final reporting package isn't just a receipt. It's a comprehensive legal and compliance tool that provides lasting peace of mind and proves your organization's commitment to data security and corporate responsibility.
Consider these documents the official conclusion to your project. They confirm that every promise of secure and responsible handling was kept. You can learn more about what goes into a hard drive destruction certificate to understand just how critical its role is. This final step ensures your IT asset removal project is a success long after the equipment is out the door.
Common Questions About IT Asset Removal
Even with a comprehensive plan, questions often arise during an IT asset removal project. Answering these upfront helps align your team and underscores why a professional, commercial-focused approach is not optional, but essential for businesses.
What Is The Difference Between IT Asset Removal And E-Waste Recycling
This is a critical distinction for any business. E-waste recycling is primarily an environmental process focused on dismantling electronics to reclaim raw materials. It is often not equipped to handle the rigorous security protocols required for corporate assets.
IT Asset Removal, also known as IT Asset Disposition (ITAD), is a security-first, comprehensive service designed for businesses. It encompasses a full chain of events: meticulous inventory tracking, certified data destruction, a documented chain of custody, value recovery, and finally, environmentally compliant recycling. If a device has ever stored corporate or customer data, a full ITAD process is mandatory to manage risk. This service is designed for commercial clients, not residential consumers.
How Can I Be Sure My Data Is Securely Destroyed
Verification should not rely on trust alone. The only way to ensure complete security is through certified documentation. A reputable ITAD partner will provide a Certificate of Data Destruction.
This is a legal document that serves as your proof of compliance. It details what was destroyed, when, and how, using methods compliant with standards like NIST 800-88. Crucially, it lists the serial numbers of every drive or device that was sanitized or physically shredded. This certificate is your official record for any audit and legally transfers liability for that data from your organization to your ITAD vendor.
Can I Get Money Back For My Old IT Equipment
Yes, and this is a significant benefit of a professional ITAD program. Many retired IT assets, even those several years old, retain considerable value. An experienced ITAD partner assesses each item based on its age, condition, specifications, and current secondary market value.
Enterprise-grade assets like recent-generation laptops, servers, and networking equipment are often excellent candidates for refurbishment and resale. The revenue generated is shared with your business, which can significantly offset or even cover the entire cost of the service.
This transforms a capital expense into a revenue stream, maximizing the return on your original investment. It is a smart financial strategy that also supports the circular economy by extending the life of functional hardware.
Contact Beyond Surplus for certified electronics recycling and secure IT asset disposal. Find out how our secure and compliant IT asset removal services can protect your United States-based business and enhance your bottom line.