For businesses in Atlanta, Georgia, upgrading technology is a constant necessity for staying competitive. But when you modernize, what happens to the old computer components? They don't just disappear. Instead, they accumulate, presenting a significant challenge that impacts data security, environmental compliance, and your company's budget. Properly managing retired IT assets isn't just about housekeeping—it's about strategic risk management for your enterprise.
The Real Problem With Old IT Hardware
That inventory of old servers, desktops, and hard drives in your Atlanta storage facility is more than just clutter; it's a potential business liability.
Every piece of retired equipment, from a data center rack to a single laptop, could still contain sensitive corporate or customer data. Furthermore, each component must be disposed of according to strict environmental regulations. A failure on either front could lead to severe financial penalties from a data breach or regulatory action.
For most Atlanta businesses, determining what to do with old computer components can seem daunting. The optimal solution is a clear, documented IT Asset Disposition (ITAD) strategy that transforms this risk into a controlled and often profitable operational function. This is about smart, secure asset management, not just disposal.
This simple decision tree breaks down the very first question your IT team needs to ask.
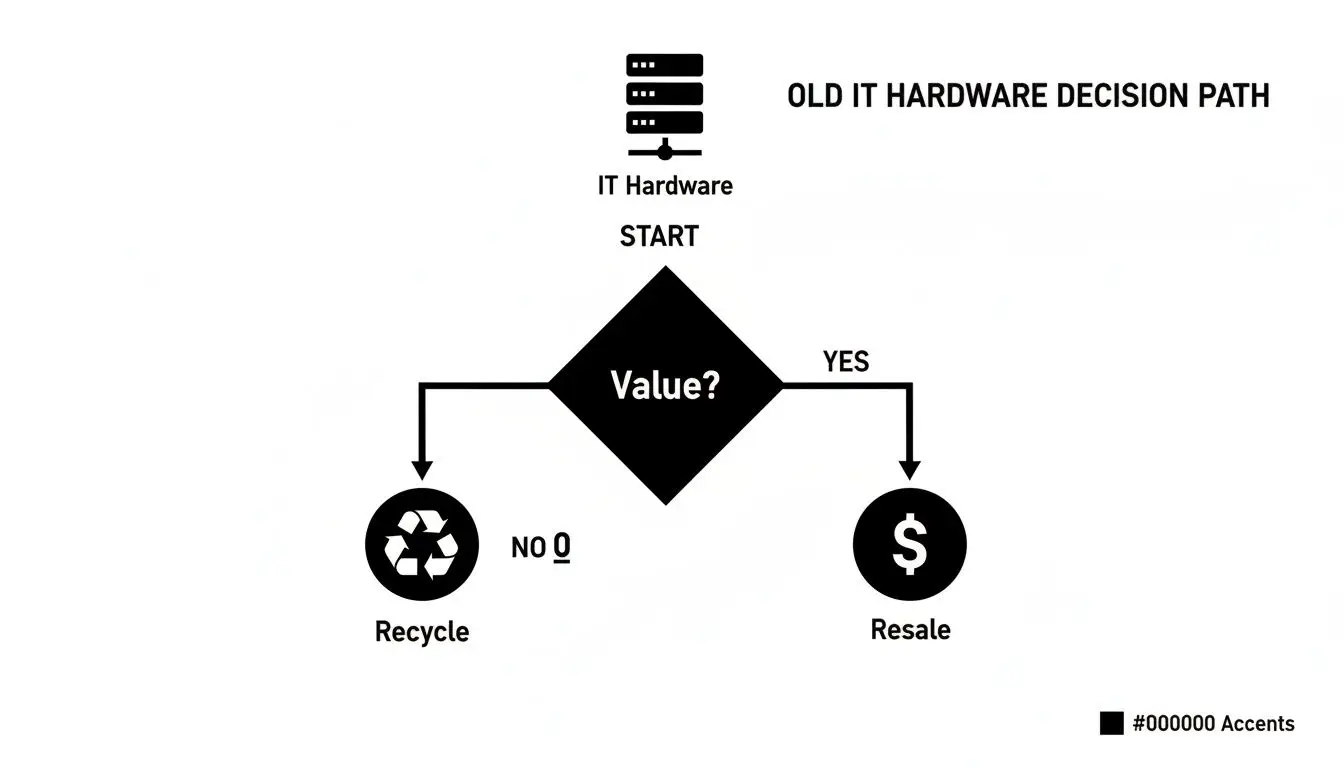
As you can see, the process begins with assessing value. This crucial step determines whether your old hardware can generate revenue through resale or if it requires secure, certified electronics recycling.
Breaking Down the Process Step-by-Step
A robust, defensible plan for managing retired IT hardware involves several critical stages. Each one is essential for keeping your Atlanta-based company secure and compliant.
- Assessment and Inventory: The process starts with a detailed audit of every component to determine its potential for resale or reuse.
- Secure Data Destruction: Before any asset leaves your facility, all sensitive data must be completely and verifiably destroyed according to standards like NIST 800-88.
- Value Recovery (Resale): Components and complete systems that retain market value can be sold through specialized IT equipment buyback programs, recovering a portion of your initial investment.
- Certified E-Waste Recycling: For equipment with no resale value, certified electronics recycling is the only way to ensure materials are processed responsibly and comply with zero-landfill policies.
This process is a core component of the larger challenge of modernizing legacy IT systems, a task every growing business must address. If your organization is currently facing a growing stockpile of equipment, our guide on what to do when old computers are piling up provides further practical advice.
To clarify your options, the table below summarizes the different disposition pathways for your old IT equipment.
At-a-Glance Options for Old Computer Components
| Disposition Pathway | Primary Goal | Best For | Key Consideration |
|---|---|---|---|
| Resale/Remarketing | Maximize financial return | Newer, high-demand, or functional enterprise equipment | Requires accurate market value assessment and certified data destruction. |
| Certified Recycling | Environmental compliance, data security | Obsolete, broken, or zero-value equipment | Must use a certified recycler (R2, e-Stewards) to avoid downstream liability. |
| Product Destruction | Brand protection, absolute security | Protototypes, recalled products, or proprietary hardware | Ensures items cannot re-enter the market; requires physical shredding. |
| Data Center Decommissioning | End-to-end project management | Complete shutdown or migration of data center facilities | Involves asset inventory, data destruction, and equipment removal. |
Each pathway serves a specific business need, and the correct choice depends on the age, condition, and type of your enterprise hardware.
Making the right choice protects your company from costly data breaches, ensures compliance with regulations like the FTC Disposal Rule, and can even turn outdated equipment into revenue.
Ultimately, this is where a certified IT Asset Disposition (ITAD) partner like Beyond Surplus comes in. A professional team handles the entire process for you—from logistics and secure data destruction to providing the Certificates of Destruction and Recycling you need for your audit trail. It transforms a nagging liability into a strategic, well-managed process.
Uncovering Hidden Value in Your Retired Components

Before you label a pallet of retired IT assets as "junk," a closer evaluation is warranted. Significant value is often hidden within old computer components, especially those from a commercial or enterprise environment. Overlooking this IT asset recovery step is equivalent to leaving money in your server room.
This initial assessment is your first move toward achieving the best financial return on your outdated technology. It helps you segregate what can be sold through an equipment buyback program from what requires certified recycling. It's a strategic process where the reward is recovered budget for your Atlanta company.
A methodical approach here ensures no valuable asset is overlooked. It can transform a disposal cost into a new revenue stream and demonstrates due diligence for regulatory compliance.
Identifying High-Value Components
Not all hardware is valued equally in the secondary market. While a five-year-old server as a whole may have limited value, its individual components could be in high demand. Your IT department should focus on identifying these specific, valuable parts.
Certain types of enterprise equipment almost always command strong resale prices, particularly if they are from recent generations and in full working order.
- Enterprise-Grade CPUs: Server processors, especially high-core-count models from Intel (Xeon) and AMD (EPYC), are always sought after for system upgrades.
- Modern RAM Modules: High-capacity DDR4 and DDR5 RAM, particularly server-grade ECC RAM, are valuable commodities. A large batch can yield a significant financial return.
- Graphics Processing Units (GPUs): High-performance GPUs from data centers or workstations are still in demand for various data processing tasks.
- Solid-State Drives (SSDs): After secure data sanitization, large-capacity enterprise SSDs are easily resold for use in other systems.
The key is to look beyond the complete system and see the potential in its individual parts. A server that is too old to meet your company's performance standards may contain thousands of dollars worth of processors and memory that are perfect for another organization's needs.
The Importance of a Detailed Inventory
Once you identify potentially valuable assets, the next critical step is creating a detailed inventory. This is not just a list; it is the master document for tracking every asset from your facility to its final disposition. A comprehensive inventory is non-negotiable for both asset value recovery and regulatory compliance.
Your inventory spreadsheet must capture key details for each component. This information is essential when requesting a quote from an ITAD partner.
Essential Inventory Fields:
- Asset Tag: Your company’s internal tracking number.
- Item Type: Be specific (e.g., Server, Laptop, CPU, RAM, Medical Equipment, Laboratory Equipment).
- Manufacturer & Model: For example, "Dell PowerEdge R740" or "Intel Xeon Gold 6248R".
- Serial Number: The unique identifier for the asset.
- Specifications: Key details like CPU speed, RAM capacity, and storage size.
- Condition: Note whether the item is functional, damaged, or untested.
This detailed preparation streamlines the entire process. When you provide a comprehensive inventory to an ITAD partner like Beyond Surplus, you give us the exact information needed to generate an accurate buyback offer, ensuring you receive the maximum possible return for your retired IT gear.
Why 'Deleting' Is Not Enough for Data Security

The old hard drives (HDDs) and solid-state drives (SSDs) your business is retiring are not just spare parts. They are archives of your operations, holding everything from employee records and financial data to proprietary intellectual property.
A common and dangerous misconception is that performing a 'quick format' or hitting 'delete' permanently erases this data. It does not. This action merely removes the pointers to the data, leaving the actual information intact and easily recoverable.
This misunderstanding places companies at severe risk. With widely available data recovery software, unauthorized individuals can easily restore "deleted" files. For a business, this is a data breach waiting to happen, potentially leading to massive fines, litigation, and reputational damage.
The Professional Standard for Data Wiping
To ensure data is irrecoverable, you must go beyond simple deletion. The professional standard is secure data wiping (or sanitization), which uses specialized software to overwrite every sector of a drive with random characters. This process is often repeated multiple times, guaranteeing the original data is permanently destroyed.
This is not just a best practice; it's a requirement for complying with data protection regulations.
- NIST 800-88: Published by the National Institute of Standards and Technology, this is the gold standard for media sanitization. Its "Purge" and "Clear" guidelines are designed to make data recovery infeasible.
- DoD 5220.22-M: This Department of Defense standard utilizes multiple overwriting passes to sanitize a drive.
Using software that adheres to these standards provides a verifiable process for data destruction. This is the correct way to protect your Atlanta business when IT equipment reaches its end of life.
When you work with a certified ITAD vendor, you should receive a Certificate of Data Destruction. This document is your proof of due diligence, confirming that all data was destroyed according to federal standards and protecting your business from potential legal and financial problems.
When to Wipe vs. When to Shred
While software wiping is ideal for drives that can be reused or resold, some situations demand a more definitive solution. For the highest level of security, nothing surpasses physical destruction.
Data Wiping (Software-Based)
- Best For: Assets with resale value, such as newer SSDs or enterprise-grade HDDs. Wiping preserves the hardware's functionality.
- Process: Overwrites all existing data with random characters, making it unrecoverable.
- Compliance: Meets key standards like NIST 800-88 and DoD 5220.22-M.
Physical Destruction (Shredding)
- Best For: Outdated, damaged, or highly sensitive drives where no risk is acceptable. It is also the only option for media like backup tapes or proprietary hardware.
- Process: The drive is fed into an industrial-grade shredder that grinds it into small fragments, making data recovery impossible.
- Compliance: This is the most complete form of destruction, exceeding all regulatory requirements.
Choosing the right method is essential for complying with regulations like HIPAA (for protected health information) and the FTC Disposal Rule. A professional ITAD partner like Beyond Surplus will assess your inventory and apply the correct, compliant method for each item, ensuring your business is fully protected.
Turning Surplus Components into Revenue
When your Atlanta business retires old computer components that retain functional value, recycling everything means forfeiting potential revenue. An IT equipment buyback program offers a superior strategy, enabling you to recover a portion of your original capital investment and convert surplus hardware into a new revenue stream.
This is a smart financial move that many organizations overlook.
Significant value can be found in your storage closets and data centers. Instead of attempting to sell items individually—a time-consuming and inefficient process—a professional ITAD partner streamlines the entire operation. It is the difference between managing dozens of uncertain transactions and executing one efficient, profitable sale.
What Makes a Component Valuable
The secondary market for IT hardware is driven by demand for reliable, enterprise-grade equipment. While not every old component is valuable, certain categories consistently retain their worth. Knowing what to identify helps focus your recovery efforts.
The most valuable assets for buyback typically include:
- Recent-Generation Servers: Complete server units, particularly from top-tier brands like Dell, HP, and Supermicro, are often sought for parts or for deployment in less demanding environments.
- Networking Equipment: Enterprise-class switches, routers, and firewalls from manufacturers such as Cisco, Juniper, and Arista remain in high demand.
- Bulk Quantities of Laptops: Large lots of identical, recent-model business laptops are ideal for buyback programs, as they can be efficiently refurbished and resold.
- High-Performance Components: As mentioned, individual parts like enterprise CPUs, large-capacity RAM modules, and GPUs can command high prices on their own.
The core principle of a buyback program is simple: it leverages the remaining useful life of your hardware. Equipment that no longer meets your company's high-performance standards is often a perfect, cost-effective upgrade for another organization.
The Strategic Advantages of an ITAD Partnership
Attempting to manage an in-house resale program creates significant logistical and security challenges. You must determine market values, find buyers, manage shipping, and—most critically—ensure every device is sanitized of sensitive data before it leaves your control.
An ITAD partner absorbs all these responsibilities into a single, integrated service.
Working with a professional firm provides clear advantages that extend beyond the final payment. The entire process is designed to be secure, transparent, and fully auditable from start to finish.
Key Benefits of a Managed Buyback Program:
- Consolidated Payment: Instead of tracking numerous small payments from different buyers, you receive one single payment for all valuable assets.
- Guaranteed Data Security: Your ITAD partner handles certified data destruction as a standard part of the process and provides a Certificate of Data Destruction for your compliance records.
- Simplified Logistics: The partner manages all pickup and transportation, removing the logistical burden from your team.
- Transparent Reporting: You receive detailed reports itemizing the value of each component, simplifying asset management and providing a clear audit trail.
This approach not only boosts your bottom line but also strengthens your company's security posture. For Atlanta businesses looking to maximize their return, exploring an IT equipment resale program is a critical step. It transforms a potential cost center into a direct financial gain.
The Responsible Choice for End-of-Life Electronics
After your inventory audit, you are left with a collection of old computer components with no resale value. What is the next step? Certified electronics recycling is the only responsible path forward for any business. Disposing of these assets in a dumpster is not just environmentally irresponsible; it is often illegal and can create significant compliance risks for your organization.
When e-waste is landfilled, toxic materials like lead, mercury, and cadmium can leach into the environment, contaminating soil and groundwater. The scale of this problem is immense. The world generated a record 62 million tonnes of e-waste in 2022—an 82% increase from 2010—yet only 22.3% was properly collected and recycled. As a UN report highlights, this waste stream is growing faster than collection efforts, making responsible disposal non-negotiable for corporations.
This is precisely why your Atlanta business must partner with a certified recycler for all IT asset disposal needs.
The Guarantee of R2 and e-Stewards Certifications
Not all recyclers operate to the same standards. To ensure your business is fully protected, you must work with a provider holding top-tier industry certifications like R2 (Responsible Recycling) or e-Stewards. These certifications are not merely marketing logos; they are your assurance that the vendor adheres to the strictest global standards for environmental safety, data security, and worker health.
A certified recycler provides a shield against downstream liability. It proves that your business took every necessary step to ensure its electronic waste was handled properly, protecting you from the legal and financial fallout of a less-reputable vendor's poor practices.
Choosing a certified partner like Beyond Surplus ensures your old components will never end up in a landfill or be illegally exported. They will enter a secure, audited process that protects both the environment and your company's reputation.
How Certified Recycling Powers the Circular Economy
Certified recycling is much more than waste management; it is an active contribution to the circular economy. Once your assets arrive at a certified facility, they are carefully dismantled in a secure environment. This is a methodical de-manufacturing process designed to recover all valuable raw materials.
Key Materials Recovered During Recycling:
- Precious Metals: Small but significant amounts of gold, silver, palladium, and platinum are extracted from circuit boards and processors for reuse in new electronics.
- Base Metals: Large quantities of copper, aluminum, and steel are recovered from wiring, heat sinks, and chassis.
- Plastics and Glass: These materials are sorted and sent to specialized processors for re-integration into various manufacturing supply chains.
This material recovery process significantly reduces the need for virgin mining, an environmentally destructive and energy-intensive activity. By reclaiming these materials, your company directly supports a more sustainable manufacturing ecosystem. You can learn more about how this process aligns with our commitment to a zero-landfill electronics recycling policy for all business clients.
Proving Your Commitment with a Certificate of Recycling
Ultimately, doing the right thing is not enough—you must be able to prove it. Upon completion of the recycling process, a certified ITAD partner will issue a Certificate of Recycling. This document is your official proof, confirming that your company’s old assets were disposed of in full compliance with all environmental regulations.
This certificate is a key asset for your Corporate Social Responsibility (CSR) reports and a requirement for any environmental or data security audit. It provides the concrete, auditable proof your stakeholders, customers, and regulators demand.
7. Locking Down the Chain of Custody for Total Accountability

From the moment your old computer components leave your Atlanta facility, their journey must be meticulously tracked. This is the chain of custody—a complete, unbroken record documenting who handled your assets, where, and when.
For any business, this is not a "nice-to-have" feature. It is an essential component of risk management and compliance with data privacy laws.
Consider the process of sending a sensitive legal document. You would not simply place it in a mailbox and hope it arrives; you would use a tracked courier service that requires signatures at every transfer point. Your IT assets demand the same level of security and accountability.
A robust chain of custody ensures your equipment is never lost, stolen, or mishandled, protecting you from a potential data breach and serving as definitive proof of compliance.
Building a Defensible Audit Trail
A secure chain of custody is built on three pillars: secure logistics, serialized tracking, and comprehensive documentation. When you partner with a professional ITAD vendor, these elements are integrated into a seamless, accountable service.
This provides you with a complete, auditable record that details how every single asset was managed from your door to its final disposition.
Key Parts of a Secure Chain of Custody:
- Scheduled Pickups: For corporate clients, the process begins with a scheduled pickup using secure, GPS-tracked vehicles and vetted personnel, ensuring safe and direct transport.
- On-Site Services: For maximum security, services like hard drive shredding can be performed at your facility. This eliminates security gaps before assets even leave your premises.
- Serialized Inventory: We create a master inventory list by scanning and logging every asset. This initial record is reconciled at every stage of the process.
A professional ITAD provider handles this entire journey for you, creating a fully auditable record. This documented process gives you peace of mind and bulletproof proof of compliance.
The Paperwork That Protects You
The documentation generated during the ITAD process is your ultimate defense in an audit. This paper trail provides clear evidence that your company adhered to all necessary data protection regulations, such as the FTC Disposal Rule or HIPAA.
Without this proof, your business remains exposed to liability. These documents officially close the loop on your responsibility for the retired assets.
Must-Have Compliance Documents:
- Transfer of Ownership: This form legally transfers custody of the assets to your ITAD vendor. Once signed, the liability for the equipment shifts from your organization to ours.
- Certificates of Data Destruction: After wiping or shredding your drives, you receive a certificate detailing which media were sanitized and the methods used, certifying that the data is irrecoverable.
- Certificates of Recycling: For all recycled assets, this document confirms they were processed in an environmentally responsible manner according to R2 or e-Stewards standards.
Together, these documents form a powerful compliance package. To understand why this final step is so crucial, learn more about what a proper certificate of destruction includes. It is the shield that proves your old computer components were managed securely and responsibly from start to finish.
Frequently Asked Questions About IT Asset Disposal
Even with a solid plan, questions often arise when it is time to retire old computer components. Here are common inquiries from IT managers and business owners in the Atlanta area, with direct, commercial-focused answers.
Can Our Business Donate Old Computers?
Donating old business computers can introduce significant data security risks. Your company remains legally responsible for any sensitive data on the devices, and most recipients are not equipped to perform certified data sanitization.
A more secure and compliant approach is to partner with a certified ITAD vendor. We can securely sanitize every device to NIST 800-88 standards, refurbish viable equipment for donation on your behalf, and responsibly recycle the remaining assets. This ensures your company's data is protected while still supporting your corporate social responsibility goals.
What’s the Difference Between R2 and e-Stewards Certifications?
Both R2 (Responsible Recycling) and e-Stewards are the premier certifications in the electronics recycling industry. Selecting a vendor with either certification guarantees partnership with a provider that meets exceptional standards for data security, environmental protection, and worker safety.
The primary difference lies in their approach to international shipments. The e-Stewards standard enforces a strict, complete ban on exporting hazardous e-waste to developing countries. The R2 standard, by contrast, permits the export of tested, functional equipment under strict control and transparency guidelines.
For your Atlanta business, engaging a vendor with either certification is a significant step up from an uncertified recycler and demonstrates a serious commitment to corporate due diligence.
How Much Does It Cost to Recycle Business Equipment?
The cost to recycle your business equipment depends on the value of the assets. It is a common misconception that IT asset disposal is always a net cost.
For businesses with newer, high-value assets—such as recent-generation servers, enterprise networking gear, or large quantities of laptops—the service can often be provided at no cost. You may even receive a payment through a robust IT equipment buyback program.
The value we recover from your valuable components is used to offset the costs of logistics, data destruction, and processing. This makes the entire process incredibly cost-effective.
For older, mixed, or lower-value equipment, a service fee based on weight or quantity may apply to cover the labor and processing costs. For organizations seeking comprehensive solutions and expert guidance on managing their retired components, exploring professional IT asset disposal services can be a crucial step. A reputable partner will always provide a transparent, detailed quote based on a complete inventory of your assets.
Contact Beyond Surplus for certified electronics recycling and secure IT asset disposal in Atlanta, Georgia. We provide transparent quotes and expert guidance to protect your business data, ensure compliance, and maximize the financial return on your retired IT equipment.