For businesses in Alabama, secure data destruction isn’t just an IT task to check off a list—it's a core component of a smart business strategy, essential for maintaining compliance and managing risk. Hitting "delete" on a file doesn't actually erase the sensitive information. It merely makes it harder to find, leaving your company wide open to vulnerabilities. This is where professional Alabama data destruction comes in, ensuring that confidential corporate, employee, and customer data is permanently and verifiably wiped from retired IT assets.
Why Professional Data Destruction is Non-Negotiable for Businesses
Deleting a file on your computer is like tearing the table of contents out of a book. While it's harder to find a specific chapter, all the pages remain for anyone determined enough to look. For a data thief, recovering "deleted" files from discarded business equipment is often a simple task. This creates an unacceptable risk for any organization handling sensitive information. A professional IT Asset Disposition (ITAD) partner provides a secure, compliant, and strategic solution to manage this risk when your enterprise electronics reach their end-of-life.

This process is about more than just disposal. It’s about treating every retired asset as a potential liability until its data is irretrievably destroyed. Failure to do so can lead to severe consequences, including staggering data breach costs, legal penalties, and damage to your company's reputation.
The Corporate Data Constantly at Risk
Consider the vast amount of confidential information stored across your organization's devices. Every server, laptop, and data center component holds sensitive data. When these assets are decommissioned, that data remains, posing a significant threat if not handled by certified professionals.
The types of business data constantly at risk include:
- Customer Information: Names, addresses, payment details, and other personally identifiable information (PII).
- Employee Records: Social Security numbers, payroll information, performance reviews, and health records.
- Financial Data: Corporate account numbers, transaction histories, budgets, and proprietary financial models.
- Intellectual Property: Trade secrets, product designs, research and development data, and strategic plans.
A single hard drive from a retired server falling into the wrong hands could expose your entire operation. This reality highlights the crucial reasons you need professional data destruction services to protect your corporate assets and maintain the trust of your clients.
To clarify these concepts, here’s a quick breakdown of key terms for your business in Alabama.
Key Data Destruction Concepts for Alabama Businesses
| Concept | Business Implication in Alabama |
|---|---|
| Data Sanitization | The process of irreversibly removing or destroying data stored on a memory device. This is your first line of defense against a breach from retired IT assets. |
| Physical Destruction | When software-based wiping isn't sufficient for compliance, physically shredding hard drives and other media ensures data can never be recovered. |
| Chain of Custody | A documented trail tracking your IT assets from the moment they leave your facility to their final disposition. It's essential for proving compliance. |
| Certificate of Destruction | A legal document provided by your ITAD vendor that serves as proof of secure and compliant data destruction. This is your official audit record. |
Understanding these terms is the first step toward building a data security strategy that truly protects your organization.
Establishing a Secure Chain of Custody for Business Assets
The moment a piece of IT equipment is slated for retirement, a secure chain of custody must be established. This is a documented trail that tracks the asset from your facility through every step of the process—transportation, data sanitization or physical destruction, and final recycling.
A certified ITAD partner provides this crucial documentation, including a Certificate of Data Destruction, which serves as legal proof that your organization met its due diligence requirements. This certificate is your best defense against claims of negligence and is essential for regulatory compliance.
Ultimately, secure data destruction isn't an expense. It's an investment in your company's security, compliance, and long-term viability. It transforms a potential liability into a managed and documented process, giving you complete peace of mind.
Staying Compliant with Alabama's Data Breach Notification Act
For any business operating in Alabama, understanding state-specific data security laws isn't just a good practice—it's mandatory. This means becoming familiar with the Alabama Data Breach Notification Act of 2018. This legislation outlines exactly how your business must protect sensitive information and what to do if a security failure occurs.
The most effective way to manage these regulations is through proactive Alabama data destruction. It is your number one strategy to prevent a data breach from retired IT assets and avoid triggering the law's notification requirements.
Effective June 1, 2018, Alabama became the 50th state to enact a data breach notification law. This law, Senate Bill 318, mandates that any business handling 'sensitive personally identifying information' of Alabama residents must implement reasonable security measures.
Crucially, it compels businesses to notify individuals if their data is compromised. The law is also explicit about handling old records—you are legally required to securely destroy them to prevent unauthorized access, even long after the data is no longer in use.
What the Law Defines as "Sensitive Data"
The act is very specific about what information requires this level of protection. A breach occurs when there is an unauthorized acquisition of what the law calls "sensitive personally identifying information" (SPII).
This term includes a person's first name or initial and last name combined with any of the following:
- Social Security number or tax ID number.
- Driver’s license number, state-issued ID card number, or another unique ID on a government document.
- Financial account numbers (like a credit or debit card) along with any required security code, PIN, or password.
- Any information about an individual's medical history or health insurance policy number.
- A username or email address, when paired with a password or a security question and answer that would allow access to an online account.
This definition covers nearly all data stored on typical business IT assets, from employee laptops and HR servers to customer databases and data center equipment.
The Financial Cost of Non-Compliance
The penalties for violating Alabama's law are significant and designed to ensure businesses prioritize data protection. If a breach occurs and your company fails to notify affected individuals in a timely manner, the financial consequences can be severe.
The Alabama Attorney General can impose a civil penalty of up to $5,000 per day for failure to issue the required notifications. This penalty is capped at $500,000 for a single breach—a substantial financial blow for any organization.
This fine does not include other associated costs, such as legal fees, credit monitoring services for victims, and the long-term damage to your company's reputation.
How Certified Data Destruction Ensures Compliance
The most effective method to comply with Alabama's law is to ensure a data breach from retired IT equipment is impossible. A certified, professional data destruction process is non-negotiable as it directly addresses the law's requirement for secure disposal of records.
When you partner with a certified ITAD vendor, you ensure that every hard drive, server, and storage device is handled according to the highest industry standards. The documentation provided is as crucial as the service itself.
Understanding the role of a Certificate of Data Destruction is essential for proving compliance. This document serves as your official legal proof of due diligence, listing asset serial numbers, destruction methods, and dates. It effectively transfers liability and demonstrates your commitment to data security, turning a potential compliance nightmare into a simple, documented, and secure process.
Choosing the Right Data Destruction Method for Your IT Assets
Once you’ve committed to securely disposing of your company's old IT equipment, the next critical question is how. This is not a one-size-fits-all decision. The optimal approach for your Alabama business depends on your security requirements, budget, and whether you want to recover value from your retired assets. Understanding your two main options—physical hardware destruction versus digital data sanitization—is the first step.
Making the wrong choice can be costly. Shredding a batch of new, functional laptops means forfeiting potential asset value. Conversely, performing a basic "wipe" on a hard drive that contained sensitive client data may not meet compliance standards, leaving your business exposed to significant risk.
This decision is especially critical when considering Alabama's data breach laws. The flowchart below illustrates the notification process if a breach occurs, reinforcing why a robust data destruction plan is your best defense.
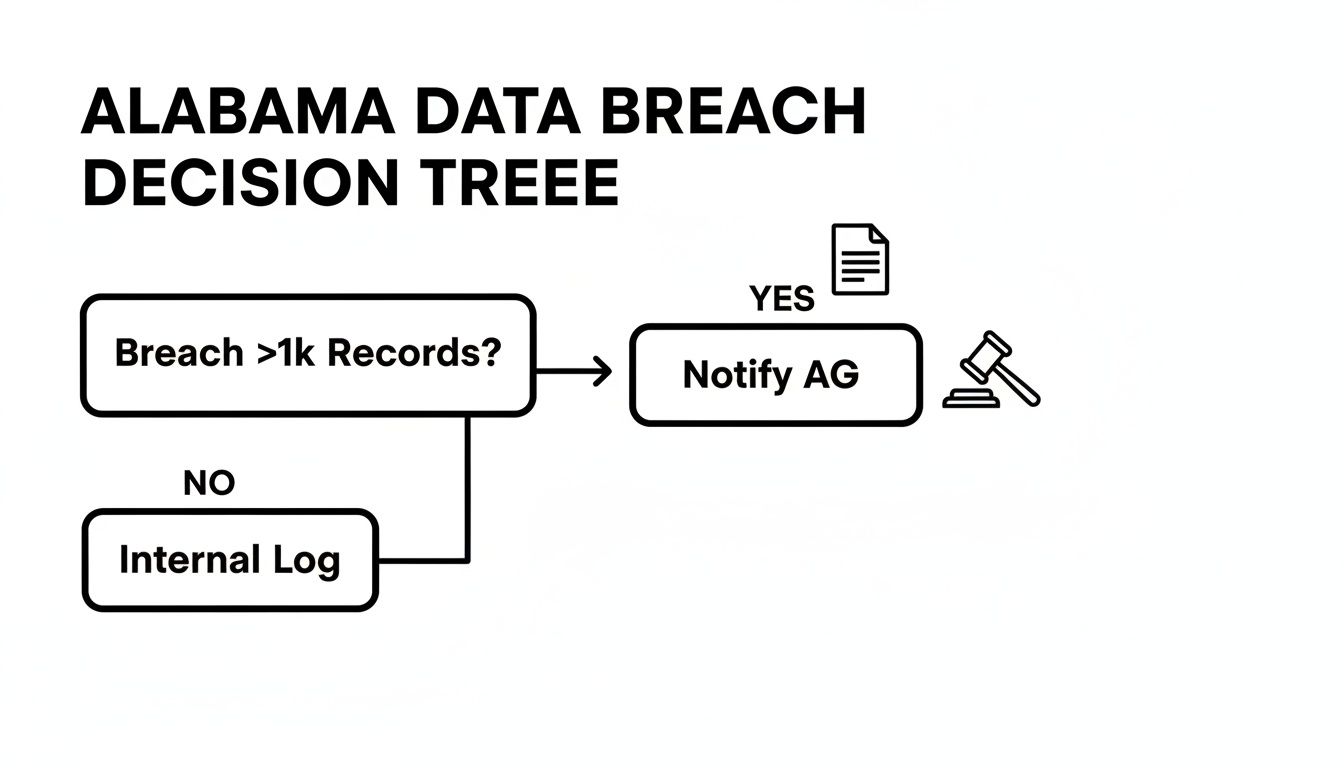
As the law states, a breach affecting over 1,000 Alabama residents requires notifying the Attorney General. It’s a situation no business wants to face, which is why certified data destruction is essential proactive protection.
On-Site vs. Off-Site Physical Destruction
For businesses requiring absolute, verifiable proof of destruction, on-site hard drive shredding is the gold standard. A mobile, industrial-grade shredder arrives at your facility, allowing you to witness every hard drive, server, and backup tape being turned into small fragments before it leaves your property. This method eliminates any chain-of-custody concerns.
The alternative is off-site shredding. Your IT assets are secured in locked containers and transported by a secure, GPS-tracked vehicle to a specialized facility for destruction. This is often a more cost-effective option for large volumes of equipment. A reputable ITAD partner will manage the process with strict security protocols and provide a complete audit trail, including a Certificate of Data Destruction for both services.
Certified Data Wiping for Value Recovery
Not all of your retired equipment needs to be physically destroyed. For newer, functional assets like recent-model laptops, servers, or smartphones, certified data wiping (or sanitization) is a smarter financial strategy. This software-based process overwrites every sector of a storage device, making the original information impossible to recover.
The industry benchmark for professional data wiping is the NIST 800-88 "Guidelines for Media Sanitization." Adhering to this protocol guarantees that data is forensically unrecoverable. Once sanitized to this standard, a device can be safely refurbished and resold, allowing your business to reclaim a portion of its initial investment.
Choosing to wipe data is both a security and a financial decision. It converts a retired asset from a disposal cost into a revenue stream, helping to offset the cost of your next technology refresh while ensuring compliance.
To help you determine the best path forward, here is a comparison of common methods.
Comparison of Data Destruction Methods
| Method | Best For | Security Level | Value Recovery Potential |
|---|---|---|---|
| On-Site Shredding | Highest-security needs; businesses requiring visual confirmation. | Maximum | None |
| Off-Site Shredding | Large volumes of obsolete or faulty media; cost-sensitive projects. | Very High | None |
| NIST 800-88 Wiping | Newer, functional devices (laptops, servers, SSDs) with resale value. | Very High | High |
| Degaussing | Magnetic media like older hard drives and backup tapes. | High | None |
Each method has a specific application. The key is to align the technique with the asset type and your organization's risk tolerance.
Making the Final Decision for Your Business
How do you choose the right method? It comes down to answering a few key questions:
- What do our internal security policies require? Some companies mandate physical destruction for any drive that stored sensitive information.
- What is the age and condition of the equipment? Newer equipment is an ideal candidate for wiping and remarketing. Obsolete or non-functional hardware should be shredded.
- Do we have specific regulatory requirements? Industries like healthcare (HIPAA) or finance (GLBA) often have strict data destruction mandates.
- Is witnessing the destruction process necessary for our compliance? If your team requires that level of assurance, on-site shredding is the only choice.
Often, the best strategy is a hybrid one. You might decide to shred all your old server hard drives but sanitize the newer laptops from your sales team to maximize both security and financial return.
To get a better feel for how these processes work in the real world, you can explore Beyond Surplus’s comprehensive security and data destruction services, designed to meet the compliance needs of businesses all across Alabama.
Protecting Your Data During Alabama's Severe Weather
Alabama's geography places it in the path of severe weather, from powerful tornadoes to destructive Gulf hurricanes. When a major storm approaches, businesses rightly focus on employee safety and operational continuity. However, the immense data security risks that storms create are often overlooked.
A natural disaster doesn't just damage buildings; it can obliterate the physical security of your entire IT infrastructure. Servers, laptops, and hard drives that were once secured can be scattered across a debris field, completely exposed. This is when a natural disaster can escalate into a full-blown data security crisis.

From Natural Disaster to Data Breach
Imagine the chaos following a tornado or major flood. Your office is damaged, and IT equipment is broken, waterlogged, and scattered. In the rush to clean up, these compromised devices become a prime target for data thieves. Even a damaged hard drive can often have its data recovered by a skilled individual.
This is not a hypothetical scenario. Alabama's history is filled with destructive storms that create these exact conditions, making businesses here particularly vulnerable. A plan to secure and destroy compromised electronics is therefore a critical component of disaster preparedness.
From 1980 to 2024, Alabama endured 116 separate billion-dollar weather and climate disasters. Events like the historic April 27, 2011, tornado outbreak highlight the immense risk of unsecured data on damaged hard drives, laptops, and servers exposed in debris fields, which can lead to major breaches during the chaos of recovery. You can discover more about Alabama's climate disaster history from NOAA.
As an IT manager, you must integrate secure e-waste management into your disaster recovery plan. A hurricane does not grant a waiver on protecting sensitive information, especially with regulations like Alabama's 2018 data breach law in effect.
Integrating ITAD into Your Disaster Recovery Plan
A comprehensive disaster recovery plan extends beyond data backups. It must include a clear protocol for managing physically compromised IT hardware. Waiting until after a storm hits to create this plan is too late.
Your plan must include these key elements:
- Immediate Asset Security: Designate a team to locate and secure all IT assets as soon as it is safe to re-enter a damaged facility. This prevents valuable hardware from being accidentally discarded with other debris.
- Secure Logistics Protocol: Your plan must outline how to transport damaged equipment securely. This involves using locked containers and maintaining a strict chain of custody, even amidst the post-disaster chaos.
- Pre-Established ITAD Partnership: Establish a relationship with a certified ITAD provider like Beyond Surplus before a disaster occurs. A pre-existing agreement ensures a rapid response for secure pickup and certified Alabama data destruction when you need it most.
- On-Site Destruction Capability: For maximum security, consider on-site shredding. A mobile destruction vehicle can come directly to your location, ensuring sensitive data is destroyed before it ever leaves your sight.
Implementing this plan transforms a high-risk, chaotic situation into a controlled, documented process.
The Role of a Certified ITAD Partner Post-Disaster
In the aftermath of severe weather, your priority is business recovery. A trusted ITAD partner removes the burden of data security from your team. They provide the expertise, equipment, and secure processes needed to handle compromised assets safely and in compliance with all regulations.
By partnering with an expert, you guarantee that every damaged device is accounted for and that all data is verifiably destroyed. This is the key to preventing a natural disaster from becoming a costly, long-term data breach that could inflict more damage than the storm itself.
When a business decides to retire a server, laptop, or phone, the first thought is usually about the data. But the physical device itself is a ticking clock of another kind. Tossing old e-waste without a plan doesn't just put you at risk for a data breach; it creates serious environmental hazards, a double-whammy that can hit your finances and your reputation hard.
Every single piece of electronic gear is packed with a cocktail of components, and many of them are hazardous. Think about the lead in old CRT monitors, mercury hiding in flat-screen displays, or the cadmium inside batteries. If that stuff ends up in a landfill, it can leach into the soil and groundwater. That kind of environmental carelessness comes with its own heavy legal and financial price tag.
The Two-Pronged Threat of E-Waste
If you don't manage your retired IT assets the right way, you're opening your organization up to two very different, but equally painful, consequences. Getting a handle on both is the only way to build a disposition strategy that’s actually secure and responsible.
- Data Security Risks: As we've covered, even a device headed for the scrap heap can be a treasure trove for data thieves. Just one forgotten hard drive can spiral into a massive breach.
- Environmental Compliance Risks: There are federal and state regulations that dictate how hazardous electronic waste must be handled. Ignoring them can lead to huge fines and cleanup bills, not to mention the kind of bad press no company wants.
A certified ITAD vendor is built to tackle both threats at once. The process always begins with secure, provable Alabama data destruction and finishes with responsible, compliant recycling of all the physical hardware.
Why Responsible Disposal Matters in Alabama
The need for certified disposal hits particularly close to home here in Alabama. The state has unfortunately been used as a dumping ground for toxic waste in the past, which makes the need for responsible e-waste management today even more critical. Decommissioned electronics don't just hold sensitive data; they contain hazardous materials that demand a certified destruction process to ensure they aren’t disposed of illegally or harmfully.
This is backed up by Alabama's own records laws for government entities, which require authorized destruction processes to stay compliant and prevent data leaks from a sloppy disposal chain. You can learn more about Alabama's records destruction requirements to see just how high the standard for compliance really is.
Choosing a certified ITAD partner gives you a secure chain of custody that protects your data from the second it leaves your building. It also guarantees the physical parts are recycled in an environmentally sound way, so your company's old assets don't end up polluting our communities.
This all-in-one approach is the only real path to complete peace of mind. It protects your most sensitive information and shows that your company is serious about its corporate social responsibility.
The True Cost of Cutting Corners
It can be tempting for some businesses to go with an informal or uncertified recycler to try and save a few dollars. This is a massive mistake.
An uncertified vendor gives you zero guarantees on data security or environmental compliance. Your company’s retired assets could be shipped overseas illegally, dumped in a local landfill, or have their data stripped and sold—leaving your organization holding the bag for all of it.
The small amount you might save with a cheap disposal service is nothing compared to the potential costs of a data breach, regulatory fines, and the permanent stain on your brand. Investing in a professional partner that provides both secure data destruction and certified Alabama e-waste disposal is, without a doubt, the most cost-effective move you can make. It turns a potential liability into a documented, secure, and environmentally responsible process.
Selecting a Certified ITAD Partner in Alabama
Choosing who handles your data destruction in Alabama is a lot more than just picking a vendor off a list. It’s about finding a partner you can trust—someone who becomes an extension of your own security team, tasked with the critical job of managing your old tech. One wrong move here can expose your business to some serious financial and reputational damage.
This isn't an area where you can afford to cut corners. The selection process needs to be thorough, focusing on a few non-negotiable criteria. A potential partner's qualifications have a direct line to your company's compliance and data security.
Essential Criteria for Vetting an ITAD Provider
When you're talking to potential partners, it's time to ask for proof. Vague promises about security just don't cut it; you need to see hard evidence of their commitment to both security and environmental responsibility.
Start with these must-haves:
- Industry Certifications: Look for credentials like R2v3 (Responsible Recycling). This certification is a clear sign that a provider is serious about environmentally sound practices and high data security standards.
- Comprehensive Liability Insurance: Make sure they have solid downstream liability insurance. This should include pollution and errors and omissions coverage to protect your business if anything goes wrong.
- Documented Chain of Custody: A reputable provider will give you a clear, documented paper trail. It should track your assets from the second they leave your office to their final destruction.
This level of scrutiny is what separates the pros from the rest and ensures you're equipped to handle the complexities of Alabama data destruction. As you begin your search, checking with a local Information Technology Services provider can be a smart first step to get a feel for the options in Alabama.
Beyond Certifications: The Partnership Approach
The best ITAD partners do more than just pick up your old equipment. They bring a strategic approach to the table, simplifying your compliance headaches and giving you total peace of mind. A big part of this is providing detailed, serialized reporting for every single asset they process.
One of the most critical pieces of this service is the Certificate of Data Destruction. Think of this as a legal document—it’s your official record proving all data was destroyed according to industry best practices and legal requirements. For any audit, this certificate is your definitive proof of due diligence.
Ultimately, you’re not just hiring a service; you’re looking for a partner who gets the unique needs of your business. You need someone who can deliver a secure, transparent, and compliant solution for your retired technology. This kind of partnership protects your sensitive information, guards your brand, and makes sure every asset is handled professionally from start to finish.
For a closer look at what a professional ITAD solution includes, feel free to explore our Alabama ITAD services designed for businesses and enterprise clients.
Got Questions About Data Destruction in Alabama? We Have Answers.
When it comes to getting rid of old IT gear, Alabama businesses have a lot of questions. That’s completely normal. Figuring out the right way to handle data security is key to building a disposal strategy that's both secure and compliant. Let's walk through some of the most common questions we hear.
What Kind of Paperwork Proves My Data is Gone for Good?
The single most important document you’ll get is a Certificate of Data Destruction. Think of it as the official death certificate for your data—it's your legal proof that you did everything right and is absolutely essential for any compliance audit.
This certificate officially passes the liability from your company to your ITAD partner. It needs to be detailed, listing things like the unique serial numbers of the devices, the specific destruction method used (like NIST 800-88 wiping or physical shredding), the service date, and a clear statement that the data is gone forever. This piece of paper is your best defense for showing you've complied with Alabama’s data breach laws and other federal rules.
Should I Choose Data Wiping or Physical Shredding?
The right answer for your Alabama data destruction plan really boils down to what you want to do with the old equipment. Both methods are highly secure, but they serve different end goals.
Here’s how to think about it:
- Data Wiping (Sanitization): This is a software-based process that follows strict NIST 800-88 guidelines to completely overwrite every bit of data on a drive. It's the perfect choice for newer, working equipment because the hardware is left intact and can be refurbished and resold. This helps you get some of your original investment back.
- Physical Shredding: This is the brute-force approach, offering the ultimate in security by literally grinding the hard drive into tiny, mangled pieces of metal. Shredding is the go-to for devices that held top-secret information, old or broken gear with no resale value, or for companies whose policies simply demand total physical annihilation.
Can I Get Secure Services in Rural Alabama?
Yes, absolutely. A good ITAD provider has logistics down to a science and covers the entire state of Alabama, not just the big cities like Birmingham or Mobile. Whether you're in a metro hub or a more remote rural town, you can and should have access to certified data destruction.
A reputable partner will arrange for secure transport, often with their own fleet or carefully vetted logistics companies. They make sure a solid chain of custody is maintained from the second the assets leave your door until they’re processed. For total peace of mind, services like on-site hard drive shredding can be brought directly to your location, no matter where you are in the state.
The real key is partnering with a provider who has a proven, documented process for secure transit. This ensures your sensitive data is protected every step of the way, regardless of your physical location in Alabama.
What's the Difference Between Data Destruction and E-Recycling?
This is a critical point that every business leader needs to grasp. Data destruction is the process of permanently and verifiably eliminating all information stored on a device. E-recycling, on the other hand, is about responsibly breaking down the physical hardware to recover valuable materials like metals and plastics while safely handling the hazardous stuff.
A true, certified ITAD service always performs data destruction first, before any recycling begins. You should never hand over IT equipment to a standard e-recycler without making sure the data has been professionally destroyed and you have the certificate to prove it. Simply recycling a device does nothing to remove the sensitive information on its hard drive.
Contact Beyond Surplus for certified electronics recycling and secure IT asset disposal. Let our experts provide you with a secure, documented, and responsible solution for your end-of-life electronics. Learn more at https://technostolic.com.