For any business thriving in Arizona's dynamic economy, data destruction is far more than just dragging files to the trash can. It is a critical security process designed to permanently obliterate sensitive information on old hard drives, servers, and other retired IT equipment. Partnering with a certified specialist for Arizona data destruction is an essential step for businesses in Phoenix, Tucson, Scottsdale, and across the state to sidestep catastrophic data breaches and maintain regulatory compliance.
Why Secure Data Destruction Is Non-Negotiable For Arizona Businesses

In a state that’s a major hub for data centers, simply hitting 'delete' on a retired computer or server is a significant gamble. "Deleted" files are often easily recoverable with basic software, leaving a trove of sensitive information exposed. Professional Arizona data destruction ensures that information is permanently eradicated—completely unrecoverable—protecting your company, your clients, and your brand reputation.
This is not just a best practice; it's a mandatory component of business operations for compliance with numerous state and federal regulations. For any Arizona business, trust is paramount, especially with the growing consumers' focus on security and identity fraud protection. A single data breach from an improperly discarded device can lead to crushing financial penalties and irreparable harm to your brand.
The Connection Between IT Upgrades and Data Security
Every time your organization upgrades its technology, a collection of outdated IT assets is created. Each retired laptop, server, or hard drive holds a piece of your company's data history. Without proper handling, that legacy data becomes a significant liability.
A strategic IT asset disposition (ITAD) plan integrates secure data destruction into the process from the very beginning, ensuring security is never an afterthought. The benefits are clear:
- Mitigating Risk: You completely eliminate the chance of a data breach from old hardware.
- Ensuring Compliance: You’ll meet the strict standards of laws like HIPAA, FACTA, and the FTC Disposal Rule.
- Protecting Brand Reputation: It shows clients and partners that you take data security seriously, building invaluable trust.
- Streamlining Operations: It makes tech refreshes and office moves a much smoother process.
When you work with a certified data destruction provider, you effectively transfer the liability tied to those old devices. They will give you a Certificate of Data Destruction, a critical document that serves as your official proof of compliance and due diligence.
Ultimately, secure data destruction is a cornerstone of modern corporate responsibility. It’s an investment in risk management that protects your digital footprint long after the physical hardware is gone. Managing this correctly goes hand-in-hand with responsible electronics recycling services in Arizona, creating a complete and secure end-of-life plan for all your technology.
The High Cost Of Improper IT Asset Disposal
When disposing of old IT assets, what you don't know can severely impact your Arizona business. Discarding an old server from a Phoenix medical office into a landfill might seem simple, but if it still contains thousands of patient records, the consequences can be catastrophic. This includes massive HIPAA fines, costly lawsuits, and a complete collapse of public trust.
Data breaches originating from improperly discarded hardware are an inevitability, not a possibility. The fallout extends far beyond a single negative news cycle—it creates long-term damage that can cripple an organization.
Financial and Legal Consequences
The most immediate impact often comes from regulatory penalties. Federal laws like HIPAA and the FTC Disposal Rule are stringent, with fines that can reach tens of thousands of dollars per violation. A single hard drive packed with unsecured data can trigger multiple violations, causing costs to escalate rapidly.
On top of fines, businesses must factor in the staggering costs of remediation, legal fees, and the potential for class-action lawsuits. These direct financial hits are typically compounded by a sharp drop in customer loyalty and revenue as trust erodes.
The Phoenix metro area is not just a desert landscape; it's a major tech hub with the second-largest concentration of data centers in the U.S. These facilities store immense amounts of sensitive data, which makes secure disposal an absolute non-negotiable. A single breach from mishandled equipment here could cost a company an average of $4.45 million—a figure that underscores the necessity of certified Arizona data destruction.
Reputational and Environmental Damage
While the financial impact is severe, the damage to your brand's reputation after a data breach can be the most difficult to overcome. Customers and partners lose faith in your ability to safeguard their information, leading directly to lost business and a tarnished public image that can take years to rebuild. A robust data destruction strategy is one of the best ways to protect your company from data breaches with secure data destruction practices.
Furthermore, improper e-waste disposal carries serious environmental liabilities. Discarding old electronics in a landfill can cause toxic materials to leach into the soil and water, potentially leading to hefty cleanup costs and fines under environmental regulations.
A certified IT Asset Disposition (ITAD) partner is your best defense, tackling both data security and environmental risks in one seamless process. This approach isn't just about checking a compliance box—it's about demonstrating corporate responsibility, protecting your bottom line, and safeguarding your brand's integrity. By choosing a vetted provider, you turn a potential liability into a strategic advantage.
Choosing The Right Data Destruction Method
Understanding your options is the first step toward building a robust data security plan for your Arizona business. Selecting the right technique ensures sensitive information is permanently eliminated, meeting both your security requirements and operational goals. The three primary methods—physical shredding, data wiping, and degaussing—each offer distinct advantages depending on the equipment and your intended outcome.
Choosing the wrong path for IT equipment disposal can lead to serious consequences. This decision tree illustrates the outcomes.
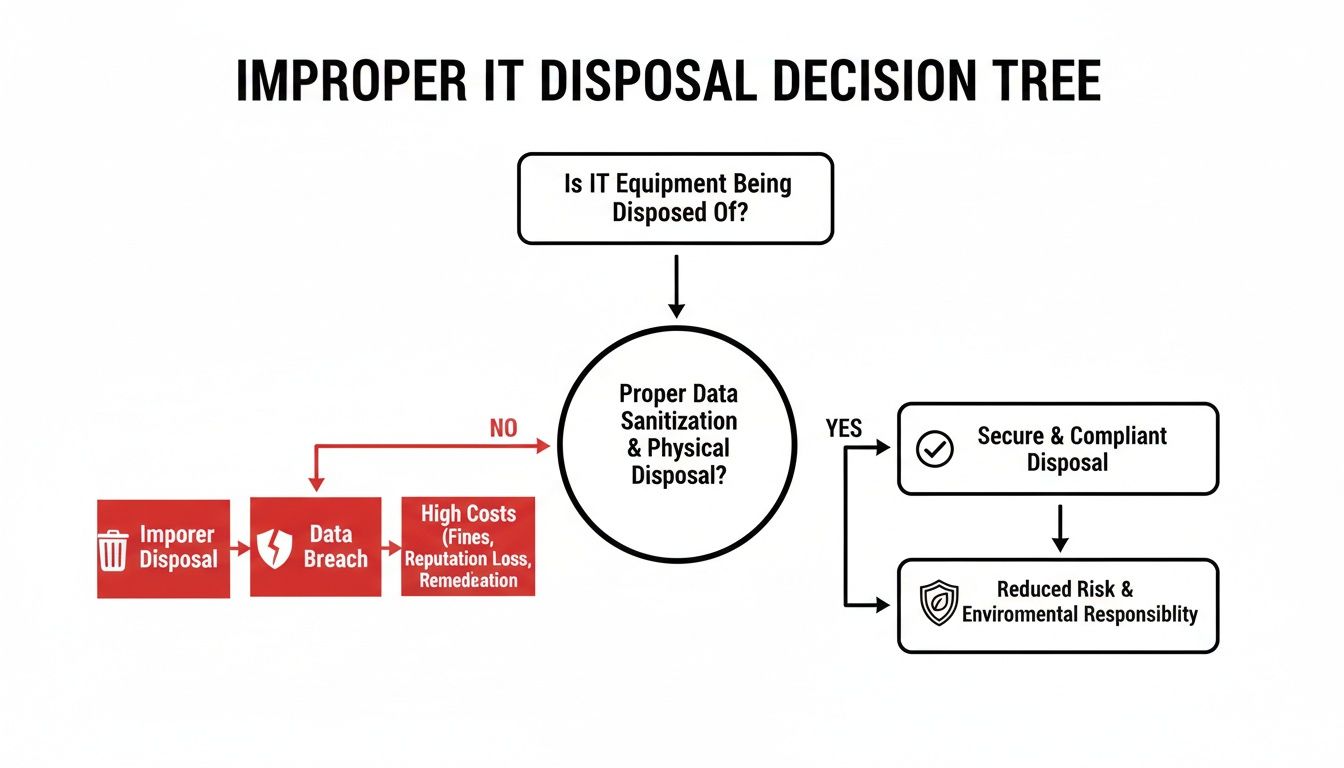
As shown, improper disposal is a direct path to data breaches and steep financial penalties, highlighting why a certified, professional process is crucial.
Physical Shredding: Absolute Data Elimination
Physical shredding is the most definitive form of data destruction. It involves an industrial shredder designed for hard drives, SSDs, backup tapes, and other media. This process reduces devices to small, mangled fragments, making data recovery physically impossible.
This method is the gold standard for organizations where maximum security is non-negotiable. If your company handles sensitive intellectual property, classified government data, or critical patient records, shredding offers undeniable proof of destruction. It is the only method to be 100% certain the data is gone forever, making it ideal for end-of-life assets with no resale value.
Data Wiping: Secure Sanitization for Asset Reuse
Data wiping, or sanitization, is a software-based method that overwrites existing data with random characters. This process is repeated multiple times until the original information is completely unreadable and forensically unrecoverable, following strict standards like NIST 800-88.
The primary advantage of data wiping is that it leaves the hardware intact and functional, allowing your business to:
- Recover value by reselling or remarketing the sanitized IT assets.
- Redeploy equipment to other departments within your company.
- Donate working hardware to non-profits and support the community.
Wiping is an excellent choice for businesses seeking to maximize return on investment from an IT refresh while maintaining stringent security protocols.
Degaussing: Magnetic Media Neutralization
Degaussing is a specialized method used exclusively for magnetic storage media, such as traditional hard disk drives (HDDs) and magnetic tapes. The process exposes the device to a powerful magnetic field, which instantly and permanently scrambles the magnetic domains where data is stored.
While extremely effective for magnetic media, degaussing renders the hard drive unusable. It is a fast and secure option, but it is important to note that it does not work on Solid-State Drives (SSDs), which store data electronically rather than magnetically.
To aid your decision, here’s a quick comparison of the three main data destruction methods. Each has its place, and the right choice depends on the asset type and your end goal.
Data Destruction Method Comparison
| Method | Process | Best For | Allows Asset Reuse? | Compliance Standard |
|---|---|---|---|---|
| Shredding | Physically destroys the device by grinding it into small, unusable pieces. | End-of-life assets, highly sensitive data, and when reuse is not a concern. | No | NA-135, DIN 66399 |
| Wiping | Software overwrites all data on the drive with random characters multiple times. | Functional assets intended for resale, redeployment, or donation. | Yes | NIST 800-88, DoD 5220.22-M |
| Degaussing | Exposes magnetic media to a powerful magnetic field, erasing all data. | Traditional HDDs and magnetic tapes requiring fast, secure destruction. | No | NSA/CSS EPL |
Ultimately, the best method depends on your specific needs. Do you require the absolute highest level of security for obsolete equipment, or are you looking to recover value from functional hardware? Answering this question will guide you to the right solution for your Arizona data destruction strategy.
For a deeper dive into these methods, you can learn more about Beyond Surplus’s comprehensive security and data destruction services.
Navigating Data Destruction Compliance Laws
For any business in Arizona, data destruction compliance is not just a recommendation—it’s a complex legal landscape that must be navigated carefully. Non-compliance can expose your organization to severe penalties, lawsuits, and significant reputational damage. The legal framework is a combination of federal mandates and state-specific laws designed to protect sensitive information.
Understanding these laws is the first step in creating a compliant IT asset disposal plan. Federal regulations like the Health Insurance Portability and Accountability Act (HIPAA) establish strict rules for patient health information. The FTC Disposal Rule dictates how businesses must handle consumer data. Both mandate that data must be rendered completely unreadable and unusable before device disposal.
The Importance of Documentation
In compliance, proof is paramount. It is not enough to claim data was destroyed; you must prove it was done correctly. This is where two key documents become your legal shield: the Chain of Custody record and the Certificate of Data Destruction.
- Chain of Custody: This is a detailed log that tracks your IT assets from the moment they leave your possession until their final destruction, ensuring no asset is lost.
- Certificate of Data Destruction: This official document from your certified vendor confirms what was destroyed, the method used, and the date of completion.
These documents are not mere paperwork; they are verifiable, auditable proof of your adherence to legal requirements. This effectively transfers liability to your certified ITAD partner, converting a routine task into a powerful risk management tool. To learn more about the standards behind this, review our guide on NIST SP 800-88 compliance.
Arizona and Federal Regulations
Arizona’s own laws add another layer of responsibility. State agencies, for example, must follow strict protocols for destroying public records. This mirrors federal requirements, where penalties for non-compliance are steep. Arizona agencies handle the disposal of non-permanent records under Arizona Revised Statute § 41-151.19, a process demanding the same diligence as federal rules like the FTC's Disposal Rule.
Mishandling electronic records on old hard drives can lead to fines of up to $43,792 per violation under FTC guidelines. You can see how these state-level requirements are managed through official records destruction processes.
A certified data destruction process isn't an expense—it's an insurance policy against catastrophic fines and brand damage. By prioritizing documented, compliant disposal, your Arizona business transforms a potential liability into a verified security protocol, protecting both your customers and your bottom line.
How To Select A Certified ITAD Partner

Choosing the right IT Asset Disposition (ITAD) partner is the most critical decision in managing your end-of-life IT assets. This choice determines whether your old equipment becomes a secure, compliant success or a significant liability.
A true expert provides more than just equipment removal. They deliver a documented, transparent, and secure service that acts as a shield for your Arizona business.
The market is filled with options, from basic recyclers to comprehensive ITAD providers. A simple recycler might dispose of your equipment, but a true ITAD partner offers a suite of services designed for corporate needs—including on-site shredding, detailed asset reporting, and value recovery programs for used technology.
Key Certifications to Look For
Certifications are not just logos; they are hard-earned proof that a vendor adheres to the highest industry standards for security and environmental stewardship. They serve as a guarantee that the provider has passed rigorous, independent audits.
Two credentials that should be non-negotiable are:
- NAID AAA Certification: This is the gold standard for secure data destruction. It verifies that a company’s hiring practices, operational security, and destruction processes meet strict protocols, ensuring your data is protected from the moment it leaves your facility.
- R2 (Responsible Recycling) Certification: This certification focuses on environmental protection, worker safety, and data security throughout the electronics recycling process. An R2-certified partner guarantees your e-waste is managed responsibly and will not be illegally dumped.
Choosing a vendor with both NAID AAA and R2 certifications ensures all bases are covered—data security and environmental compliance. This dual certification is the hallmark of a top-tier provider.
Essential Questions to Ask Potential Vendors
Before signing a contract, it is essential to vet potential partners. Their answers to key questions will reveal the quality and security of their operations.
Start by inquiring about their chain-of-custody procedure. How do they track your assets from your location to their final disposition? A reliable partner will provide serialized tracking and detailed reports without hesitation.
You should also inquire about their employee screening and training programs, as the individuals handling your sensitive assets are a critical link in the security chain.
Finally, always request a sample Certificate of Data Destruction to ensure it contains the level of detail required for your legal and auditing needs. Getting clarity on these points is central to finding the right provider for your company's comprehensive Arizona ITAD services.
Integrating Data Destruction Into Your Disaster Recovery Plan
What happens to your sensitive business data when disaster strikes? In Arizona, businesses face risks from wildfires, flash floods, and severe storms that can destroy an entire IT infrastructure. In the aftermath, you are left with damaged servers, melted hard drives, and vulnerable storage media.
While most disaster recovery plans focus on data backup and restoring operations, many overlook a critical final step: data destruction. Ignoring this can turn a natural disaster into a devastating data breach. Damaged hardware may seem useless, but it remains a potential goldmine for data thieves if not handled with immediate, certified security.
Preparing for the Unexpected
A crisis leaves no time for planning. That is why you must integrate IT asset disposition (ITAD) into your business continuity strategy before an event occurs. The goal is to have a clear, step-by-step process ready for the secure and compliant disposal of any compromised assets. This foresight prevents a chaotic situation from becoming a security nightmare.
Your plan should include these key steps:
- Secure the Site: Immediately control access to the compromised location to prevent unauthorized removal of sensitive IT assets.
- Asset Inventory: Quickly create a detailed list of all damaged hardware, noting serial numbers to establish a solid chain of custody.
- Emergency Contact: Have a pre-vetted, certified ITAD partner on standby, ready to deploy for emergency pickup and destruction.
Having a nationwide ITAD partner on call means you can manage the crisis with confidence. It ensures that even in the worst-case scenario, your most valuable digital assets are protected from exposure and your business remains compliant.
From Natural Disaster to Data Security Crisis
This threat is not merely theoretical. Arizona has experienced dozens of billion-dollar weather and climate disasters, from massive wildfires to severe droughts that put data centers and offices at physical risk. As documented by NOAA, these events are increasing in frequency and severity.
You can explore the data on these climate events in Arizona to understand the tangible risk.
When hardware is damaged by fire or water, it is often a total loss for business operations, but the data inside can often still be recovered. These compromised servers and drives demand immediate, certified physical destruction, such as shredding. It is the only way to ensure a natural disaster does not evolve into a legal and financial catastrophe fueled by a data breach.
Answering Your Arizona Data Destruction Questions
When disposing of old IT equipment, many questions arise. It is wise to be cautious—your data is on the line. Here are straightforward answers to common questions from Arizona businesses.
Wiping vs. Shredding a Hard Drive: What’s the Difference?
Think of it this way: data wiping is like professionally cleaning a house for a new occupant, while shredding is like demolishing the house entirely.
Data wiping uses specialized software to overwrite every bit of data on a hard drive, making the original information unrecoverable. This is the ideal choice if you intend to reuse the hard drive or resell the computer, thereby preserving its value.
Conversely, shredding is complete physical destruction. The hard drive is fed into an industrial shredder that reduces it to small, unrecognizable metal fragments. There is no recovery from this process. Shredding offers the highest level of security and is the standard for drives that contained highly sensitive information.
Is a Certificate of Data Destruction Really Required in Arizona?
Yes, absolutely. For any business handling sensitive customer or company data, a Certificate of Data Destruction is non-negotiable.
This document serves as your official proof of compliance with federal laws like HIPAA for medical data or the FTC Disposal Rule for consumer information. It is the auditable record that demonstrates due diligence and officially transfers liability for the destroyed data from your company to your certified vendor. Without it, you have no way to prove proper handling during an audit.
Can You Destroy Our Data at Our Facility in Arizona?
Yes. Any reputable IT asset disposal (ITAD) vendor will offer on-site services, bringing a mobile shredding truck directly to your office or data center.
This service offers a significant benefit, as you and your team can physically witness the destruction of your hard drives and other media. It provides an unbroken chain of custody and ultimate peace of mind. For businesses where security is the top priority, on-site service is the recommended solution.
For certified Arizona data destruction and secure electronics recycling designed for your business, you can count on the experts. Contact Beyond Surplus today to schedule a pickup or request a quote, and ensure your company's data remains protected. Find out more at https://technostolic.com.