Your network team needs capacity. Finance wants restraint. Operations won't tolerate delays. That's exactly why procurement teams keep searching for used telecom equipment for sale.
That search is reasonable. It can also go badly if you buy on price alone.
The secondary market is no longer a fringe channel. The refurbished networking equipment market was valued at USD 145.5 billion in 2024 and is projected to reach USD 170.52 billion by 2033, growing at a 4.6% CAGR, and telecom operators accounted for over 63% of global revenue in 2023 according to Custom Market Insights on the refurbished networking equipment market. Serious operators use refurbished infrastructure because it can solve real budget and availability problems.
The mistake is treating this as a bargain hunt. It isn't. It's a risk management exercise that touches performance validation, supportability, data security, and legal liability. If you're buying for healthcare, finance, education, government, or any multi-site enterprise, the seller's process matters as much as the hardware itself.
A procurement manager who understands IT asset disposition will make better buying decisions because used telecom gear usually has a prior life, prior owners, and prior compliance exposure.

An Introduction to Buying Used Telecom Equipment
Buying used telecom gear makes sense when you need to expand, replace failed components, support legacy environments, or avoid waiting on new hardware pipelines. Cisco routers, optical transport shelves, Nokia components, line cards, power supplies, and carrier switches all circulate through the secondary market for one reason. Enterprises still need them.
That doesn't mean every listing is safe to buy.
A smart buyer separates three questions that too often get blended together:
- Will it work: Has the seller tested ports, modules, optics, fans, and power input under load
- Will it fit: Does the firmware, part number, and hardware revision match your current environment
- Will it expose us: Can the seller document sanitization, handling history, and chain of custody
Buy used equipment only when the seller can prove condition, provenance, and process. If they can prove only price, keep walking.
The Strategic Case for Refurbished Hardware
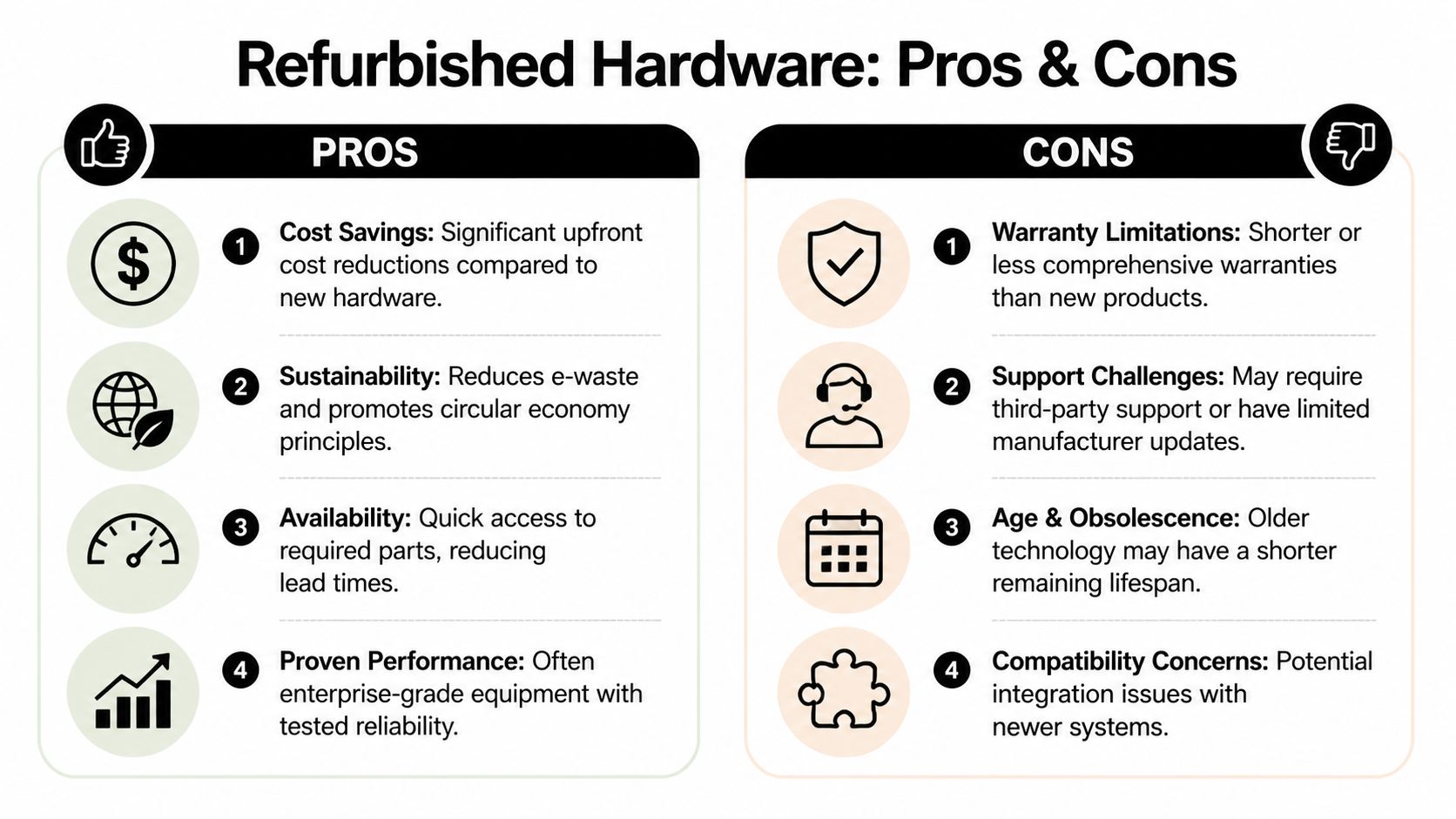
The best argument for refurbished hardware isn't thrift. It's control.
When procurement buys correctly, refurbished telecom assets can compress deployment timelines, preserve capital, and keep legacy platforms operational without forcing a full forklift upgrade. That's useful when you're extending service life in branch environments or filling a specific gap in a core network.
Where refurbished equipment helps
The financial case is strong. Refurbished telecom equipment can offer cost recovery of up to 90% compared to new purchases, while still supporting identical functional capacity in carrier-grade deployments, according to PICS Telecom on refurbished telecom equipment. If your team needs a line card, transport component, or replacement switch now, that kind of cost flexibility changes the discussion.
It also supports circular procurement. Reuse keeps equipment in service instead of pushing everything immediately into scrap channels. That's one reason many organizations now connect buying decisions to broader circular economy electronics practices.
The practical advantages usually look like this:
- Budget relief: You can allocate less to replacement hardware and keep capital available for security, modernization, and labor.
- Faster sourcing: Secondary suppliers often have inventory that OEM channels don't have available on your timeline.
- Legacy continuity: Older platforms still running production workloads can stay supported longer with spare components.
- Operational flexibility: You can buy test stock, cold spares, or interim gear without overcommitting to a full refresh.
Where buyers get burned
Refurbished doesn't automatically mean validated. Some sellers clean the chassis, boot the unit, and call it done. That's not refurbishment. That's resale with a nicer label.
The weak points are predictable:
- Support limitations: OEM support may be restricted or unavailable, forcing you into third-party maintenance.
- Short remaining life: Older equipment may function today but offer a narrower runway for updates and replacement parts.
- Compatibility friction: Wrong firmware, wrong hardware revision, or region-specific variants can create deployment issues.
- Security exposure: Poorly handled decommissioned equipment can carry unresolved data and compliance problems.
Practical rule: If you're buying refurbished gear for production, require testing records that map to the functions you actually depend on. A boot screen isn't a test plan.
The right stance is disciplined, not skeptical. Used telecom equipment for sale can be a strategic advantage. It becomes a liability when your team treats it like a commodity.
Key Equipment Types and Inspection Essentials
Some categories deserve much tighter inspection than others. If you apply the same checklist to a router, an optical shelf, and RAN hardware, you'll miss real risks.
The market is large and still expanding. The global telecom equipment market is projected to reach USD 942.76 billion by 2031, with RAN equipment holding 33.02% share in 2025, while coherent optical transport is forecast to grow at a 9.32% CAGR through 2031, according to Mordor Intelligence on the telecom equipment market. That matters because the secondary market will keep seeing supply from these categories.

Routers and switches
For Cisco, Juniper, Alcatel, or similar platforms, start with basics and then get specific.
- Part number validation: Match the exact SKU, revision, and license implications to your approved bill of materials.
- Port testing: Ask whether every copper, fiber, uplink, and management interface was verified.
- Power and cooling: Confirm fans, power supplies, and alarms were tested under sustained runtime.
- Firmware integrity: Verify the software path you'll need after deployment. If your team manages Cisco gear, this guide on resetting a Cisco switch is a useful reminder that configuration state and access method matter during evaluation.
A cosmetic grade tells you almost nothing about internal reliability.
Optical transport gear
Optical hardware needs more than a visual once-over. WDM shelves, transponders, muxponders, and coherent optics can fail in ways that aren't obvious until installation.
Check these points:
- Connector condition matters. Scratched or contaminated fiber interfaces create avoidable signal issues.
- Module matching matters just as much. Make sure optics, cards, and chassis revisions are compatible.
- Alarm history should be available if the seller tested the shelf.
- Faceplate and slot damage can indicate rough removal or improper storage.
RAN and access equipment
RAN hardware moves in volume, but buyers should be careful. Radio units, baseband components, and associated accessories often depend on tightly matched deployment scenarios.
If the seller can't explain the source environment, storage conditions, and validation method for RAN gear, assume you're taking integration risk they haven't priced in.
For this category, ask for mounting hardware details, outdoor exposure history, connector condition, and confirmation that serials and labels remain legible. Traceability matters.
Your Due Diligence Checklist for Vetting Sellers
A router arrives on time, powers on, and passes a basic bench check. Two weeks later, your security team finds retained credentials and old configuration data still on the unit. At that point, the problem is no longer price or availability. It is audit exposure, liability, and a seller that failed to control the chain of custody.
That is why seller review deserves the same discipline as hardware validation. Procurement teams that focus only on model numbers and discounts miss the bigger risk. Used telecom equipment can carry residual data, weak traceability, and undocumented handling. If the seller cannot prove how the asset was received, sanitized, tested, and transferred, you are buying operational risk along with the hardware.
Reseller accountability on data security remains a weak point in this market. Sellers often market inventory and pricing, while giving little attention to documented sanitization practices such as NIST 800-88. For regulated buyers, equipment without a certified data destruction history creates direct compliance and liability exposure, as described in BrightStar Systems coverage of used telecom equipment.
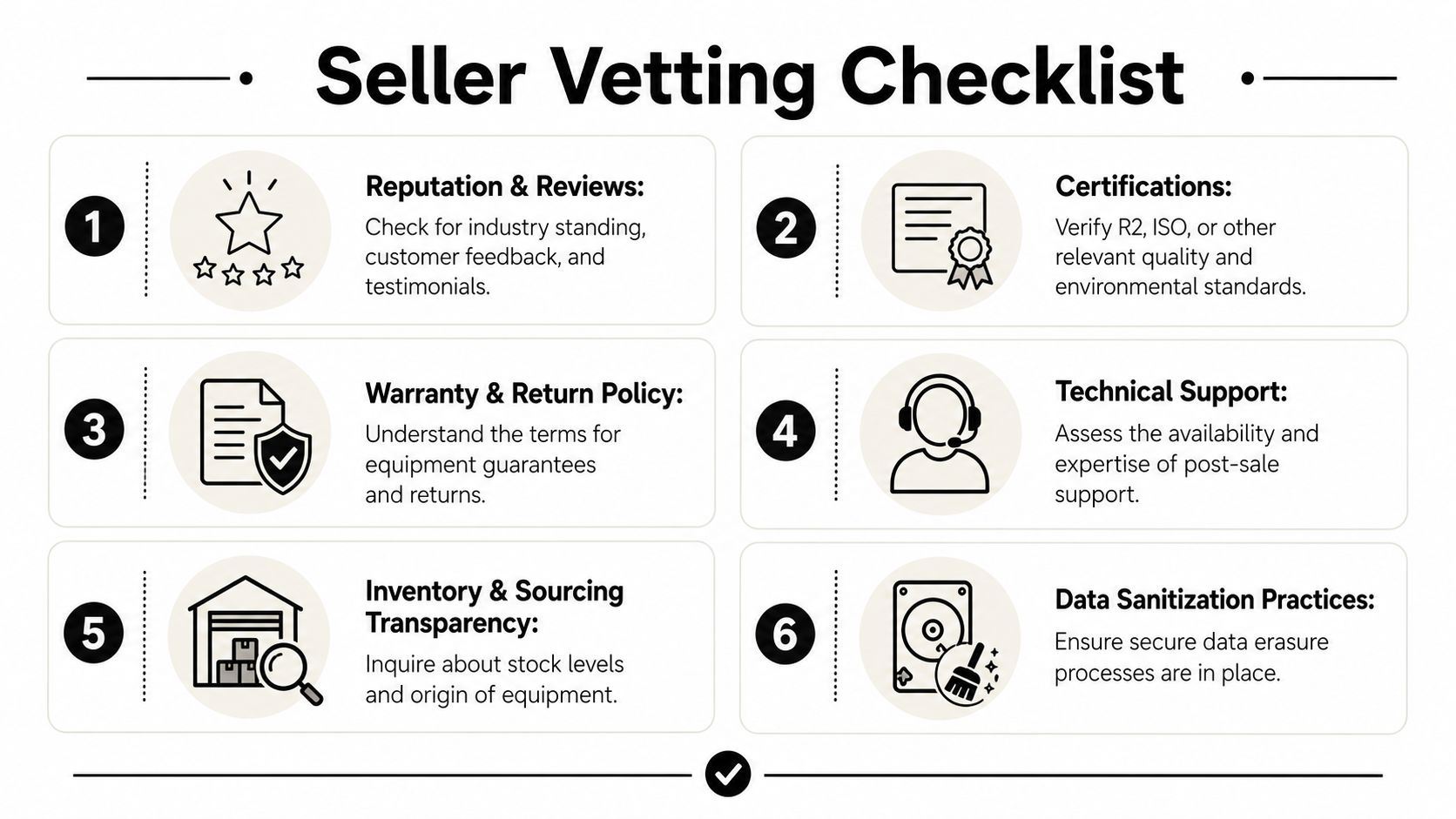
Demand documents, not promises
A seller's claims do not reduce your risk. Documentation does.
Use a vendor due diligence checklist for ITAD and equipment sellers and require evidence before issuing a purchase order:
- Certificate of data destruction: Get proof that any storage media or retained data was sanitized through a documented process.
- Chain of custody records: Confirm who handled the asset, where it was stored, and when control changed hands.
- Testing documentation: Require specific validation results, not vague phrases like "pulled from working environment."
- Return and warranty terms: Get written remedies for dead-on-arrival units, early-life failures, and mismatched parts.
- Asset identification: Tie serial numbers, model numbers, revision details, and condition notes to the invoice.
If those records are missing, treat the asset as unverified.
Know what compliance liability looks like
Telecom equipment is not always stateless hardware. It may retain configuration files, credentials, call records, logs, customer data, or operational metadata. In healthcare, finance, education, and government, that exposure can trigger reporting obligations, legal review, and internal control failures.
Ask these questions in writing:
- Was the equipment sanitized to a recognized standard such as NIST 800-88 or DoD 5220.22-M?
- Did the seller perform sanitization in-house or outsource it?
- Will the seller provide certificates tied to serial numbers?
- Is there documented transfer of custody from previous owner to reseller to buyer?
- What is the written remedy if residual data is discovered after delivery?
A vague answer is an answer. Remove the seller from consideration.
Separate brokers from process-driven vendors
Brokerage access has value. It does not replace process control.
A process-driven vendor should explain intake, asset identification, storage controls, sanitization, testing, packing, and shipment procedures in plain language. You should hear a repeatable workflow, not sales talk. The safer seller is the one that can show how equipment moved from decommissioning to resale with records at each step.
Beyond Surplus is one example of this category. It provides certified data destruction, certificates of recycling, and chain-of-custody documentation as part of ITAD and buyback workflows. That is the standard procurement teams should require from any seller or recovery partner.
Red flags that should end the conversation
Do not negotiate past basic control failures.
| Red flag | Why it matters |
|---|---|
| Vague testing language | Usually signals limited validation or inconsistent process |
| No serial-level documentation | Weak traceability and poor audit support |
| No sanitization proof | Creates data exposure and compliance risk |
| Auction-style "as is" terms for production purchases | Pushes nearly all failure risk to the buyer |
| Inconsistent part descriptions | Increases the odds of mismatch, substitution, or revision conflict |
Cheap hardware with weak documentation is expensive hardware.
Pricing Models and Calculating Total Cost of Ownership
Procurement teams often compare quote to quote and miss the actual question. What will this equipment cost to own, integrate, support, and retire?
That blind spot is common because leading resellers often fail to provide quantitative TCO models comparing used vs. new equipment, leaving buyers without a clear view of hidden costs such as integration and warranty issues, and without quantifiable environmental value for reuse in ESG reporting, according to Salvex listings commentary on secondary equipment market gaps.
What belongs in your TCO model
You don't need invented formulas. You need discipline.
Include these factors every time:
- Acquisition cost: Unit price, lot pricing, and shipping
- Testing and staging labor: Internal bench time, imaging, compatibility checks, rack prep
- Support cost: Third-party maintenance, spares strategy, replacement turnaround
- Deployment risk: Downtime exposure if a component fails or arrives mismatched
- Exit value: Potential resale, buyback, or recycling path at end of life
In this situation, IT asset lifecycle management becomes useful. Buying, operating, and retiring the asset should be one financial model, not three separate decisions.
Sample TCO Comparison New vs. Used Router
| Cost Factor | New Router (OEM) | Refurbished Router (Certified Reseller) |
|---|---|---|
| Purchase price | Higher upfront cost | Lower upfront cost |
| Lead time impact | May be longer depending on channel availability | Often faster if in stock |
| Internal testing | Usually lighter if standard build | Often heavier to confirm fit and firmware |
| Support model | OEM warranty and support path | Third-party support or reseller warranty |
| Integration risk | Lower if fully standardized | Depends on validation and compatibility checks |
| End-of-life recovery | Possible through ITAD or trade-in | Possible through ITAD, resale, or recycling |
Cheap hardware with expensive integration work isn't cheap. Build the labor and support assumptions before you sign the PO.
The environmental side belongs in the model too, even if your seller can't quantify it cleanly. Reuse can support sustainability goals, but don't accept vague ESG language in place of documentation.
Post-Purchase Support and End-of-Life Planning
A good purchase decision includes the exit plan on day one. If you wait until the equipment is obsolete, you'll recover less value and create more internal work.
Start with support. Decide whether the hardware will sit in a lab, run as a cold spare, or support production traffic. That determines how much post-purchase coverage you need. For production use, define your replacement path, sparing policy, and service escalation before deployment.

Build the end-of-life plan into the purchase
Here, disciplined buyers outperform reactive ones.
Partnering with a certified ITAD vendor for IT buyback models enables organizations to monetize decommissioned infrastructure while ensuring compliance with regulations like the FTC Disposal Rule through certified data destruction and transparent chain-of-custody documentation, according to CES Telecom information on IT buyback and compliance. That means your used purchase shouldn't be treated as a dead-end asset. It should have a documented recovery path.
Use a simple operating model:
- Tag assets clearly: Keep serials, install locations, and ownership records current.
- Track configuration changes: Good records reduce resale friction and support decommissioning.
- Separate reusable from obsolete gear: Some assets belong in remarketing channels. Others belong in certified recycling.
- Require end-of-life documentation: Certificates matter when audit, legal, or compliance teams ask questions later.
Procurement should ask one final question before buying. Who will take this equipment back, document sanitization, and help recover residual value when we're done with it?
If you can't answer that before purchase, the lifecycle plan is incomplete.
Frequently Asked Questions for Enterprise Buyers
Can used telecom equipment go into production environments
Yes, if your team validates compatibility, defines support coverage, and buys from a seller with documented testing and traceability. Don't put uncertified gear into production just because the price looks attractive.
What matters more, hardware condition or seller process
Seller process. A scratched chassis is usually manageable. Missing chain-of-custody records, vague sanitization claims, and weak return terms are much more dangerous.
What should regulated industries demand before purchase
Healthcare, finance, education, and government buyers should require documented sanitization history, serial-level records, chain of custody, and clear liability transfer language. If the seller can't provide those, the equipment shouldn't enter your environment.
Should we buy single units or stage a larger lot purchase
For a new seller, start with a controlled purchase. Validate packaging quality, serial accuracy, testing consistency, and support responsiveness. Then scale.
How do we handle mixed fleets with legacy and current platforms
Standardize the approval process around part-number accuracy, firmware path, and support ownership. Mixed environments fail when teams buy ad hoc parts without a consistent intake and validation workflow.
Is auction inventory a good idea for enterprise procurement
Sometimes, but only for noncritical use cases or highly experienced teams. Auction terms often shift risk to the buyer, and documentation can be thin. For production deployments, documented refurbishment and sanitization matter more than opportunistic pricing.
What's the smartest buying posture
Treat used telecom equipment for sale as a strategic sourcing category, not a side market. Build policy around compliance, testing evidence, supportability, and end-of-life recovery. That will protect your budget and your organization.
If you're evaluating used telecom equipment and need a process-driven ITAD partner, contact Beyond Surplus for certified electronics recycling, secure data destruction, IT buyback support, and documented chain-of-custody services that help reduce procurement and compliance risk.