For any business, irreversible data destruction isn't just a best practice—it's a critical component of corporate security and risk management. When it comes to guaranteeing that sensitive enterprise data is gone forever, nothing surpasses the finality of secure hard drive shredding. Unlike software-based wiping, which can sometimes leave recoverable data fragments, physical shredding completely annihilates storage media, turning drives into a pile of useless, irrecoverable scrap.
This guide is designed for business owners, IT managers, and facility managers who are responsible for the secure disposal of corporate IT assets.
Why Physical Destruction Is Your Strongest Defense
Simply deleting files or reformatting a hard drive at its end-of-life is a significant security oversight. This common mistake ignores the principle of data remanence—the residual magnetic traces of information that persist on storage platters even after deletion. For a determined data recovery specialist, these digital remnants are a potential gateway to your company's most valuable secrets.
Physical destruction is the only absolute solution. It functions like an industrial-strength paper shredder for your most confidential digital documents, but one engineered to pulverize solid steel and electronic components. This process doesn't just erase data; it destroys the physical medium where the data resided, making recovery impossible.
This level of security is a core business necessity, not a luxury. Demand for professional data destruction services is growing as more enterprises recognize the severe risks associated with improper data disposal. The market for hard drive shredding is projected to expand from USD 0.72 billion to USD 1.2 billion by 2033. This growth is driven by increasing cyber threats and stringent regulations like the FTC Disposal Rule, which legally mandates the permanent destruction of sensitive consumer data.

The Absolute Certainty of Shredding
For IT executives and business leaders, the objective is not just data removal but absolute, verifiable certainty. Secure hard drive shredding provides precisely that, eliminating any possibility of a data breach from retired IT assets. It is a non-negotiable step in any comprehensive IT asset disposition (ITAD) strategy.
Key benefits for your business include:
- Permanent Data Elimination: Once a drive is processed through an industrial shredder, the data is forensically unrecoverable by any known technology.
- Compliance and Risk Mitigation: It provides a legally defensible process that meets strict regulatory standards, protecting your company from substantial fines and legal action.
- Protection of Intellectual Property: Your trade secrets, customer databases, and internal financial records are destroyed permanently, with zero chance of future exposure.
Ultimately, choosing to shred is a strategic decision to safeguard your company's reputation, maintain customer trust, and secure your digital legacy. Understanding what to do with old hard drives allows your organization to build a more robust security posture. Physical destruction delivers the peace of mind that comes only from knowing your sensitive information is permanently gone.
Choosing Your Method: Shredding vs. Wiping
Selecting the appropriate data destruction method is a strategic choice based on the future of the IT asset. The central question is not merely "how do we destroy the data?" but rather, "what is the intended disposition of the hardware?" This distinction is critical for maximizing security and the financial return on your IT investments. The correct decision depends entirely on whether a device is slated for reuse or for permanent retirement.
When Data Wiping Makes Financial Sense
Certified data wiping is the optimal choice for IT assets that retain functional value and are intended for reuse, resale, or donation. This software-based process overwrites every sector of a hard drive with random binary data, effectively sanitizing the original information while preserving the hardware's physical integrity and functionality. This method is ideal for:
- Lease returns: Ensuring all corporate data is removed before equipment is returned to the leasing company.
- Employee redeployment: Safely reassigning laptops and workstations within your organization.
- IT asset resale: Maximizing ROI on retired servers, laptops, and networking gear through the secondary market.
By preserving hardware functionality, certified wiping contributes directly to your company's bottom line and sustainability objectives, converting potential e-waste into a recoverable asset.
Data wiping is an act of value preservation. It securely sanitizes an asset, unlocking its potential for remarketing and cost recovery, which is a core principle of an effective IT Asset Disposition (ITAD) strategy.
When Shredding Is the Only Answer
Conversely, secure hard drive shredding is the definitive, final solution for assets at the absolute end of their lifecycle. This method is not about preservation; it’s about total, irreversible annihilation. If a drive contains top-tier sensitive data, is physically damaged, or is simply too old to be reused, shredding is the only way to guarantee a 0% chance of data recovery.
Shredding is the non-negotiable choice for:
- End-of-life drives: Obsolete or failing hard drives that have no resale value.
- Damaged media: Drives that are physically broken and cannot be accessed by wiping software.
- Highest-security data: Devices containing intellectual property, patient records (HIPAA), or financial data (GLBA) where any risk is unacceptable.
It provides absolute peace of mind by physically destroying the storage platters, turning them into small, unrecoverable fragments of metal. For a detailed guide on the sanitization process, you can explore more on how to completely clean a hard drive before making a final decision on destruction.
A Side-by-Side Comparison
To help you build a blended strategy that fits your specific needs, here’s a straightforward comparison of the two methods.
Comparing Data Destruction Methods: Shredding vs. Wiping
| Factor | Secure Hard Drive Shredding | Certified Data Wiping |
|---|---|---|
| Security Assurance | Absolute (100% Unrecoverable): Physical destruction offers the highest level of security. | High (NIST 800-88 Compliant): Data is effectively erased, but the physical drive remains. |
| Asset Value | Eliminated: The drive is destroyed and its value is reduced to scrap metal. | Preserved: The hardware remains fully functional and ready for resale or reuse. |
| Best Use Case | End-of-life, damaged, or highly sensitive data-bearing assets. | Functional assets intended for remarketing, redeployment, or donation. |
| Compliance Proof | Certificate of Destruction | Certificate of Data Erasure |
| Environmental Impact | Materials are responsibly recycled after destruction. | Promotes a circular economy by extending the life of electronic devices. |
An intelligent ITAD program utilizes both methods strategically. Wiping recovers value from viable assets, while shredding provides an ironclad security guarantee for all other media. This dual approach ensures your organization is both financially prudent and completely secure.
On-Site vs Off-Site Shredding: Which Is Right for Your Business?
The location where your data is destroyed is as crucial as the method itself. For secure hard drive shredding, businesses can choose between two primary service models: on-site and off-site destruction. The optimal choice depends on your organization's security protocols, compliance requirements, and operational preferences. Understanding the specifics of each approach will enable you to align your data destruction plan with your corporate governance policies.
On-Site Shredding: Maximum Security and Witnessed Destruction
On-site shredding represents the highest level of security for businesses that cannot tolerate any chain-of-custody risk. A specialized, industrial-grade shredding vehicle comes directly to your corporate facility or data center. Your hard drives are destroyed on your premises before ever leaving your control. Your team can witness the entire process, from serial number scanning to the final destruction, providing direct verification that the data is gone for good.
This method is standard for industries handling highly sensitive information:
- Healthcare: Provides clear proof of HIPAA compliance through witnessed destruction of drives containing patient records.
- Finance and Legal: Protects client financial data and privileged information in line with regulations like GLBA.
- Government Agencies: Essential for classified or confidential data where no margin for error is acceptable.
By eliminating the transportation of live data, on-site shredding removes all risk of in-transit loss or compromise.
Off-Site Shredding: Secure and Cost-Effective Logistics
Off-site shredding offers a highly secure, auditable, and more economical alternative suitable for many enterprise applications. In this model, your hard drives are collected from your location in locked, tamper-evident containers and transported securely to a specialized destruction facility. These facilities are designed for secure data destruction, featuring 24/7 surveillance, strict access controls, and audited procedures. A rigorous chain of custody is maintained from collection to destruction, with every step meticulously documented.
While the shredding occurs at a separate location, the security protocols are equally stringent. GPS-tracked vehicles and detailed asset tracking ensure your media is accounted for throughout the process, providing a robust and defensible audit trail.
For off-site shredding, secure transport is paramount. It is essential to engage a certified ITAD partner like Beyond Surplus that guarantees your sensitive assets are handled with the highest security standards. To learn more about local options, check out our secure hard drive shredding service to see how we manage this process.
How to Choose the Right Shredding Option
Selecting between on-site and off-site shredding requires balancing security needs, budget, and operational convenience. There is no single "best" answer—only the most appropriate fit for your company’s specific requirements.
Consider these factors when making your decision:
| Consideration Factor | On-Site Shredding (Mobile) | Off-Site Shredding (Plant-Based) |
|---|---|---|
| Security Focus | Maximum: Eliminates all transit risk; ideal for ultimate peace of mind and direct verification. | High: Relies on a secure, documented chain of custody and a controlled facility environment. |
| Cost | Premium Service: Higher cost due to the logistics of bringing specialized equipment and personnel to your location. | More Economical: Lower operational costs for the vendor result in more competitive pricing. |
| Compliance Needs | Easiest to Verify: Witnessed destruction offers simple, direct proof for auditors and stakeholders. | Fully Compliant: Provides a Certificate of Destruction and a complete, verifiable audit trail. |
| Convenience | Minimal Disruption: The process is completed quickly and efficiently at your facility. | Effortless: Requires only scheduling a secure pickup; the vendor manages all subsequent logistics. |
| Volume of Assets | Suitable for any volume, but the premium price is most justified for high-security projects. | Often more practical and cost-effective for large-scale or routine disposals. |
Ultimately, both on-site and off-site services from a certified provider like Beyond Surplus deliver the same outcome: your data will be completely and permanently destroyed, and you will receive a Certificate of Destruction as proof. The right path is the one that best aligns with your company's risk management strategy, budget, and internal policies.
Inside the Secure Shredding Process
What exactly occurs after your enterprise hands over its retired hard drives to a professional shredding service? This is not an arbitrary act of destruction but a meticulously managed and documented procedure designed to ensure absolute security and provide a robust audit trail. Understanding these steps demonstrates why partnering with a certified provider is essential for corporate compliance. The entire system is built around an unbreakable chain of custody, a formal record that tracks your devices from collection to final destruction.
The Initial Steps: Secure Collection and Inventory
The process begins with a secure collection. Whether for on-site or off-site shredding, trained technicians arrive at your facility to gather the designated equipment. Drives are placed into locked, tamper-evident containers to prevent unauthorized access during handling. A critical component of this stage is the creation of a detailed inventory. Each hard drive's unique serial number is scanned, creating the first entry in the chain-of-custody log. This serialized tracking is non-negotiable for true accountability and provides a direct link between the physical asset and its digital record.
This visual flow chart breaks down the key stages of the secure shredding journey, from collection all the way to the final destruction options.
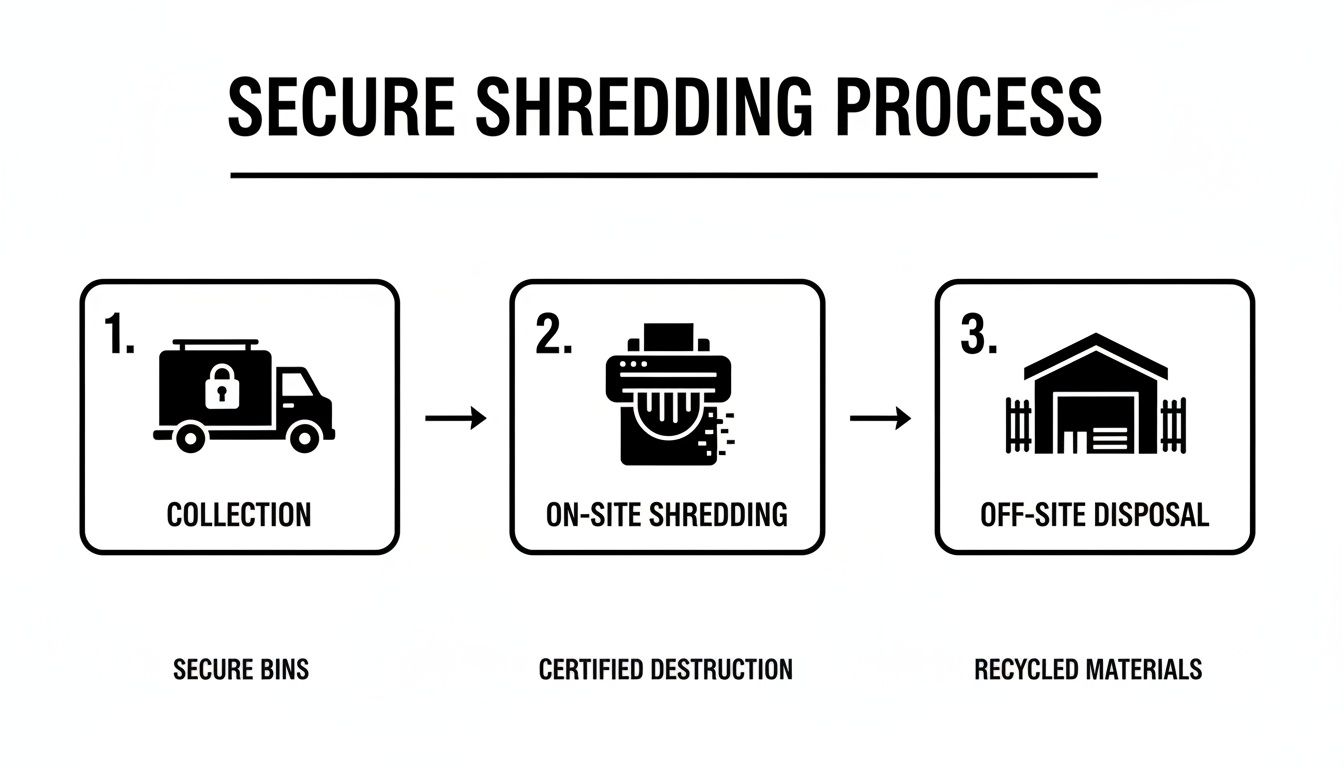
As the infographic illustrates, the process diverges based on your service choice: immediate, witnessed destruction via on-site shredding, or the secure, facility-based off-site alternative.
The Mechanics of Destruction
Once inventoried and secured, the drives proceed to destruction. Industrial-grade shredders employ powerful rotary blades to shear, tear, and grind the metal and electronic components into small, mangled fragments. The defining metric of effective shredding is the final particle size. Industry standards, such as those set by the NAID (National Association for Information Destruction), dictate how small these fragments must be to render data recovery impossible. For hard drives, this typically means shredding them into pieces smaller than 2 inches in diameter, making it physically impossible to reconstruct the platters.
The objective of secure hard drive shredding is not merely to break the drive but to obliterate the data-bearing platters so completely that no forensic technology on earth can reconstruct the information. This level of physical finality is what separates professional shredding from any other disposal method.
Finalizing the Process: The Certificate of Destruction
After the final drive has been destroyed, the most critical step for your records is the issuance of a Certificate of Destruction. This is not a simple receipt but a formal legal document that serves as your official proof of compliant data disposal.
This certificate will always include:
- A unique serial number for the certificate itself.
- The date and location of the destruction.
- A detailed list of the shredded items, often including their serial numbers.
- The name of the vendor that performed the service.
- A statement confirming that assets were destroyed in accordance with industry standards.
This document officially transfers liability for the data from your organization to the shredding vendor. It is your ultimate defense in an audit or legal proceeding, proving you exercised due diligence to protect sensitive information as required by regulations such as the FTC Disposal Rule, HIPAA, and GLBA.
Meeting Compliance and Managing Business Risk
Viewing secure hard drive shredding as a mere IT cleanup task is a critical business error. It is a fundamental practice of modern corporate governance and risk management. Failure to properly destroy data on retired equipment represents a direct threat to your business, with physical shredding serving as your final and most reliable defense against data breaches that can lead to severe fines, litigation, and reputational damage.
Data disposal regulations are not suggestions; they are legal mandates with significant penalties for non-compliance. A single corporate hard drive improperly discarded, still containing customer or employee data, can place your company in direct violation of state and federal laws, leading to financial penalties that can reach millions of dollars.

Navigating Key Data Protection Regulations
Several major regulations mandate how businesses must handle and dispose of sensitive information. IT managers and business owners responsible for hardware decommissioning must be familiar with these rules.
- The FTC Disposal Rule: This federal rule requires businesses to take "appropriate measures" to dispose of sensitive information derived from consumer reports, making the data unreadable and unreconstructable.
- HIPAA (Health Insurance Portability and Accountability Act): For any organization handling Protected Health Information (PHI), the HIPAA security rule requires policies for the final disposition of electronic PHI and the hardware on which it is stored. Shredding is an established method for rendering PHI unusable.
- GLBA (Gramm-Leach-Bliley Act): Financial institutions are governed by the GLBA Safeguards Rule, which mandates the protection of consumer financial data. This includes a written security plan that covers the secure disposal of customer information.
Ignoring these standards can lead to audits, severe fines, and public breach notifications, causing irreparable harm to your brand's reputation.
The Certificate of Destruction: Your Legal Shield
This is where shredding transitions from an operational task to a powerful risk management tool. After your hard drives are destroyed, a certified vendor like Beyond Surplus provides a Certificate of Destruction. This formal document is your legally defensible proof of compliance.
A Certificate of Destruction isn't just paperwork. It is a legal instrument that formally transfers liability for the data from your organization to your certified ITAD partner. It serves as irrefutable evidence in an audit or legal proceeding that you took deliberate, professional steps to protect sensitive information.
This certificate officially closes the loop on an asset's lifecycle, providing a clear, documented end to your responsibility for the data it once held. This transforms secure hard drive shredding from a simple expense into a critical investment in your company’s security and legal protection. You can learn more about how this aligns with government standards in our guide on NIST SP 800-88 compliance.
Why NAID AAA Certification Is the Industry Benchmark
To ensure your data destruction process is defensible under scrutiny, it is imperative to partner with a NAID AAA Certified vendor. This certification is the gold standard in the information destruction industry. It signifies that a provider has successfully passed rigorous, unannounced audits conducted by independent security professionals.
These audits verify every aspect of the operation against the highest industry standards:
- Hiring Practices: All employees with access to sensitive materials undergo extensive background checks.
- Operational Security: The entire process, from pickup to destruction, follows strict protocols to maintain a secure chain of custody.
- Facility Security: Destruction plants are equipped with 24/7 monitoring, controlled access, and continuous surveillance.
Choosing a NAID AAA Certified partner like Beyond Surplus ensures you are engaging a security expert committed to a process that withstands the most stringent legal and regulatory challenges. It is the highest assurance that your business, your customers, and your bottom line are protected.
Your Top Hard Drive Shredding Questions, Answered
Even with a clear understanding of the process, practical questions often arise when developing a secure IT asset disposal plan. Getting direct answers to these common inquiries is key to making a confident, informed decision. Here, we address the most frequent questions from IT managers and business owners about secure hard drive shredding.
What Types Of Devices Can Be Shredded?
Secure shredding is not limited to traditional spinning hard disk drives (HDDs). Industrial-grade technology is designed to destroy nearly any data-bearing device, ensuring comprehensive security across all retired corporate IT assets.
Professional shredders can destroy:
- Solid-State Drives (SSDs): These are pulverized to destroy the integrated memory chips where data is stored.
- Backup Tapes: LTO, DLT, and other magnetic tape formats are shredded into unusable fragments.
- USB Flash Drives: The internal memory chips are obliterated, ensuring permanent data destruction.
- Smartphones and Tablets: Mobile devices are physically destroyed to prevent access to their internal storage.
- Optical Media: CDs, DVDs, and Blu-ray discs are shattered, making data recovery impossible.
A certified ITAD partner like Beyond Surplus can process mixed batches of these devices in a single service, streamlining your end-of-life asset management.
Do I Need to Erase Data Before Shredding?
No. This is one of the primary advantages of physical destruction. There is no need to invest time or resources in wiping drives before they are shredded. The shredding process itself is the ultimate form of data sanitization.
The mechanical act of shredding physically annihilates the storage platters or memory chips, making all data permanently unrecoverable by any means. This provides a secure and efficient solution, especially for non-functional or damaged drives that cannot be accessed by software-based wiping tools.
This approach frees up your IT team's time and guarantees that even non-functional drives or devices that fail to power on are disposed of with the highest level of data security.
What Happens to the Shredded Materials?
After your hard drives and other media are reduced to small, unrecognizable fragments, the focus shifts from data security to environmental responsibility. The resulting material is not sent to a landfill. Instead, the shredded e-waste is securely transported to a certified downstream recycling partner. At these specialized facilities, the raw materials are sorted and processed for reuse.
- Commodity Separation: Metals like aluminum, steel, and copper are separated from plastics and circuit board components.
- Responsible Recycling: These recovered materials are reintroduced into the manufacturing supply chain, reducing the need for virgin resource extraction.
- Environmental Standards: The entire process adheres to strict environmental regulations and certifications, such as R2 (Responsible Recycling), ensuring a sustainable end-of-life for your IT assets.
This commitment ensures your data destruction process is not only secure but also aligns with corporate sustainability initiatives.
How Is the Cost of Hard Drive Shredding Determined?
Pricing for secure hard drive shredding is generally transparent and based on several key factors. Understanding these variables helps with budgeting and service selection. For a deeper dive, check out our analysis of hard drive shredding costs and what influences them.
The primary cost determinants are:
- Quantity of Drives: Pricing is often structured per drive or by total weight. Unit costs typically decrease as the volume of drives increases.
- Service Model: On-site shredding is a premium service and generally costs more than off-site shredding due to the logistical requirements of mobilizing a shredding vehicle and crew.
- Location: Your geographic location can influence pricing due to transportation costs and local market rates.
- Reporting Requirements: Detailed reporting, such as serialized asset tracking and logging, may incur an additional fee for the meticulous inventory management involved.
- Additional Services: Pricing can be affected if shredding is bundled with other ITAD services, such as full-scale electronics recycling, asset removal, or data center decommissioning.
Working with a professional provider ensures you receive a clear, customized quote based on your specific project requirements, with no hidden fees.
Contact Beyond Surplus for certified electronics recycling and secure IT asset disposal. For businesses across the United States seeking a certified partner for secure data destruction and electronics recycling, Beyond Surplus offers comprehensive solutions tailored to your compliance and security needs. Learn more at https://technostolic.com.